简介
官方地址
- Spring Cloud Gateway建立在Spring Boot 2.x,Spring WebFlux和Project Reactor之上,需要 Spring Boot 和 Spring Webflux 提供的 Netty 运行,它不能在传统的Servlet容器中工作,也不能在作为WAR构建时工作
- 网关里引入其它模块包含spring-boot-starter-web的需要排除
yaml配置
# 访问信息 server: address: 0.0.0.0 port: 8800 servlet: contextPath: / spring: # 服务名称 application: name: springCloudGateway # SpringCloud配置 cloud: # TODO 网关配置 gateway: # 路由机制 discovery: locator: # true 默认路由机制 # 开启服务注册和发现功能,服务网关自动根据服务发现为每一个服务创建一个路由,这个路由将以(大写服务名)开头的请求路径转发到对应的服务中 # 访问地址:127.0.0.1:8800/大写服务名/服务上下文/Controller/Method # # false 关闭默认路由机制,需要手动配置routes,默认通过路由名进行跳转的方式将失效,将请求路径上的服务名配置为小写 # 访问地址:127.0.0.1:8800/小写写服务名/服务上下文/Controller/Method enabled: false lower-case-service-id: true # 路由地址 routes: - id: BFF-AUTH-ROUTE # 自定义路由id,全局唯一(基于 【BFF-AUTH】 服务的路由) uri: lb://bffAuth # 路由跳转到的服务名称,如果是多个服务则会进行负载均衡(默认随机策略,也可设置成权重策略) predicates: # 断言,拦截请求规则设置 - Path=/springCloudGateway/auth/ filters: - StripPrefix=1 # 过滤掉第一个路径的值 - RewritePath=/auth/(?<segment>.*),/bffAuth/$\{
segment} # 路径重写:将 /auth/ 重写为 /bffAuth/ 讯享网
跨域配置
讯享网/ * @描述: 全局网关跨域 TODO 如果每个服务上面配置了跨域,那么就需要把那些配置删掉 * @作者: lixing * @日期 2021/6/16 9:48 */ @Configuration public class GlobalCorsConfig {
/ * @描述 跨域配置 * @作者 lixing * @日期 2021/6/22 17:43 */ private CorsConfiguration buildConfig() {
CorsConfiguration corsConfiguration = new CorsConfiguration(); // 预检请求的缓存时间(秒),即在这个时间段里,对于相同的跨域请求不会再预检了 corsConfiguration.setMaxAge(18000L); // 允许cookies跨域 corsConfiguration.setAllowCredentials(true); // 允许向该服务器提交请求的URI,*表示全部允许,在SpringMVC中,如果设成*,会自动转成当前请求头中的Origin corsConfiguration.addAllowedOrigin("*"); // 允许访问的头信息,*表示全部 corsConfiguration.addAllowedHeader("*"); // 允许提交请求的方法类型,*表示全部允许 corsConfiguration.addAllowedMethod("*"); return corsConfiguration; } / * @描述 自定义跨域过滤器 * @作者 lixing * @日期 2021/6/22 17:49 */ @Bean public CorsWebFilter corsFilter() {
UrlBasedCorsConfigurationSource source = new UrlBasedCorsConfigurationSource(new PathPatternParser()); source.registerCorsConfiguration("/", buildConfig()); return new CorsWebFilter(source); } }
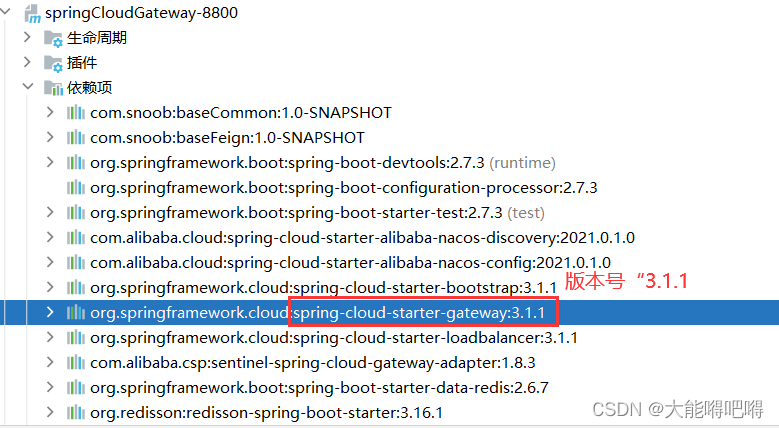
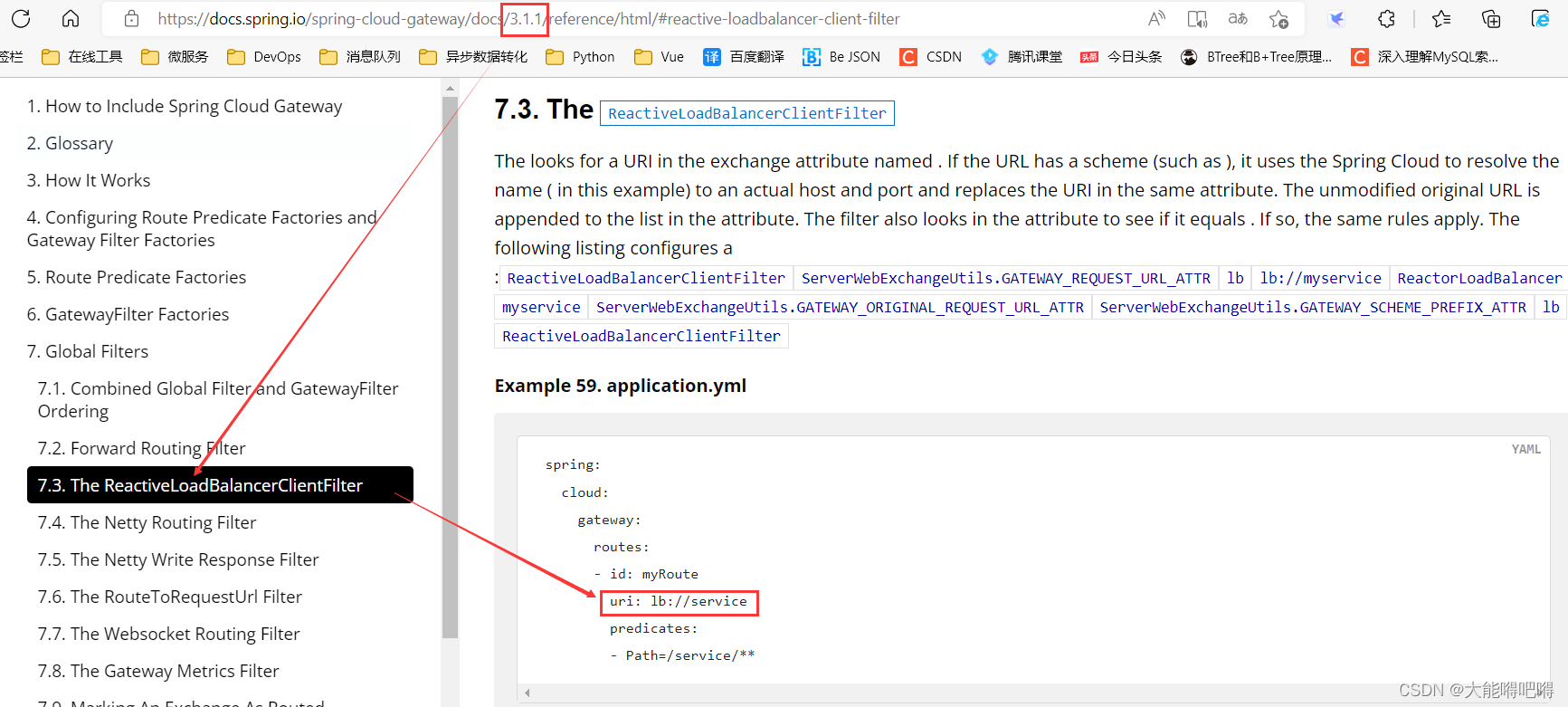
负载均衡配置
根据负载均衡发生位置的不同,可以分为"服务端负载均衡"和"客户端负载均衡" 1、客户端负载均衡是指:在发生请求之前就已经选举出了即将请求的服务实例,在微服务调用关系中一般会选择该方式 pom依赖
讯享网<!-- Springcloud2020开始弃用了Ribbon,因此Alibaba在2021版本nacos中删除了Ribbon的jar包,改用SpringCloudLoadbalancer 来实现负载均衡 --> <!-- FIXME ========================================================================= SpringCloudLoadbalancer --> <dependency> <groupId>org.springframework.cloud</groupId> <artifactId>spring-cloud-starter-loadbalancer</artifactId> </dependency>
yml配置
spring: # 服务名称 application: name: springCloudGateway # SpringCloud配置 cloud: # TODO nacos配置中心、注册中心 nacos: server-addr: 192.168.213.148:8848 # nacos访问地址 username: nacos # nacos登陆账号 password: nacos # nacos登陆密码 config: # nacos中配置文件的读取方式:${spring.application.name}-${spring.profile.active}.${spring.cloud.nacos.config.file-extension} # 默认Nacos的配置文件会覆盖本地的配置文件 context-path: /nacos # 访问地址 namespace: b2d90f05-6fb6-4735-a1c7-c4ed2e4587d2 # 命名空间(对应开发环境) group: springcloudalibaba # 所属分组(对应开发项目的别名) file-extension: yaml # 配置文件后缀 discovery: namespace: b2d90f05-6fb6-4735-a1c7-c4ed2e4587d2 # 命名空间(对应开发环境) group: springcloudalibaba # 所属分组(对应开发项目的别名) # TODO loadbalancer负载均衡 loadbalancer: enabled: true # 默认打开loadbalancer负载均衡策略 nacos: enabled: false # 默认关闭nacos负载均衡策略 # TODO 网关配置 gateway: # 路由机制 discovery: locator: # true 默认路由机制 # 开启服务注册和发现功能,服务网关自动根据服务发现为每一个服务创建一个路由,这个路由将以(大写服务名)开头的请求路径转发到对应的服务中 # 访问地址:127.0.0.1:8800/大写服务名/服务上下文/Controller/Method # # false 关闭默认路由机制,需要手动配置routes,默认通过路由名进行跳转的方式将失效,将请求路径上的服务名配置为小写 # 访问地址:127.0.0.1:8800/小写写服务名/服务上下文/Controller/Method enabled: false lower-case-service-id: true # 路由地址 routes: # TODO 基于 【BFF-AUTH】 服务的路由配置 - id: BFF-AUTH-ROUTE uri: lb://bffAuth predicates: - Path=/springCloudGateway/auth/ filters: - StripPrefix=1 - RewritePath=/auth/(?<segment>.*),/bffAuth/$\{
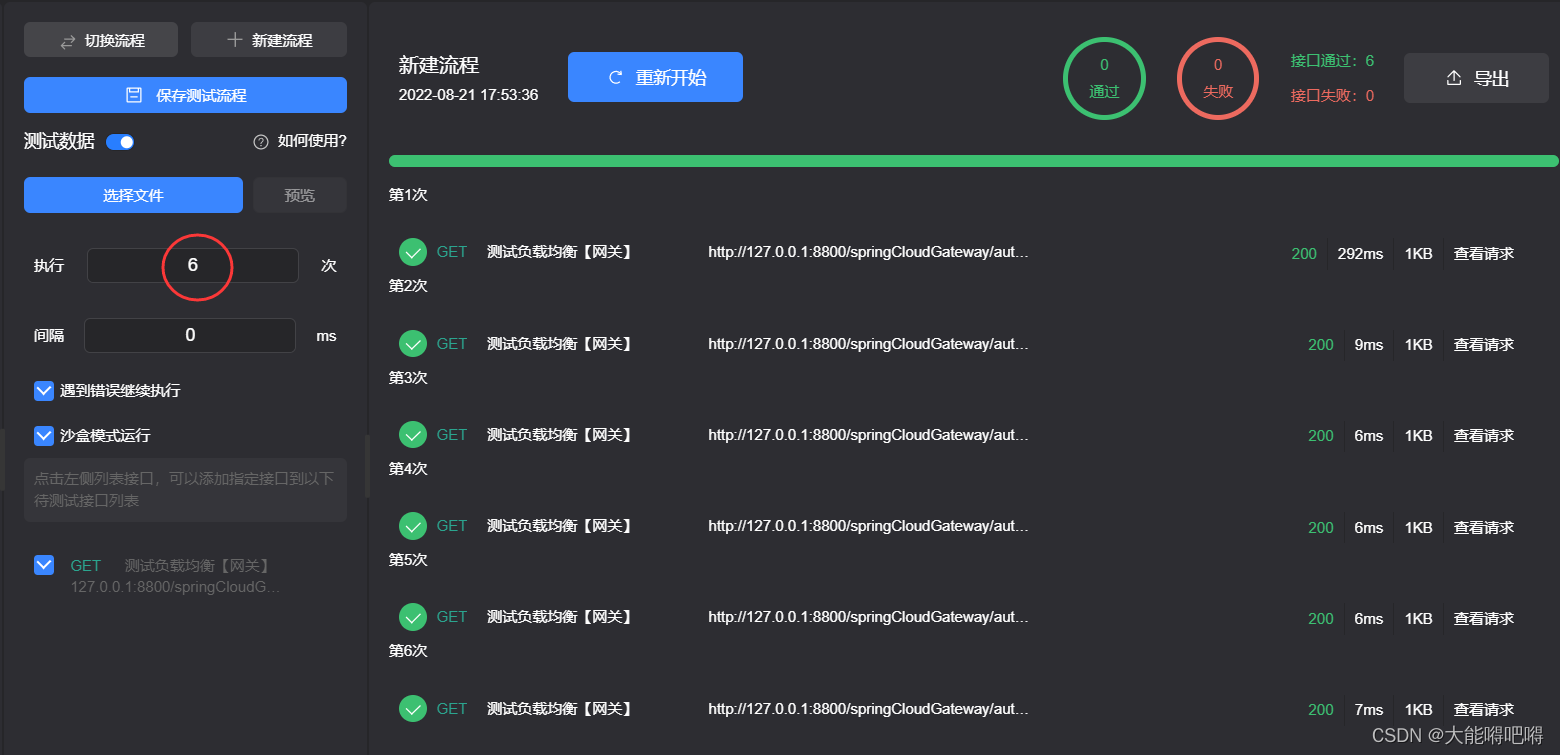
segment} 测试(默认采用的是随机策略)

网关Filters限流
讯享网1、通过网关过滤器的方式进行限流比较单一,灵活性差 2、接口触发限流,直接返回409错误码,对前端很不友好,后台需要重写代码,成本比较高
Java代码
package com.springcloudalibaba.gateway.configurer; import com.springcloudalibaba.bclass.base.BaseLoginUserInfo; import com.springcloudalibaba.bclass.enums.SysKeyEnum; import com.springcloudalibaba.bclass.util.JwtUtil; import com.springcloudalibaba.bclass.util.StrUtil; import org.springframework.cloud.gateway.filter.ratelimit.KeyResolver; import org.springframework.context.annotation.Bean; import org.springframework.context.annotation.Configuration; import org.springframework.context.annotation.Primary; import org.springframework.stereotype.Component; import org.springframework.web.server.ServerWebExchange; import reactor.core.publisher.Mono; import java.util.Objects; / * @描述: 基于SpringCloudGate网关的Filer过滤器对请求进行限流 * @作者: lixing * @日期 2021/7/17 14:20 */ @Component @Configuration public class RequestRateLimiterForGatewaySentinelRouteConfig {
/ * @描述 获取请求用户ip作为限流key * @作者 lixing * @日期 2021/7/17 14:21 * @Param [] * @return org.springframework.cloud.gateway.filter.ratelimit.KeyResolver * * 配置方法:参考网关过滤器的 RequestRateLimiter 配置项 */ @Bean public HostAddressKeyResolver hostAddressKeyResolver() {
return new HostAddressKeyResolver(); } / * @描述 获取请求用户id作为限流key * @作者 lixing * @日期 2021/7/17 14:22 * @Param [] * @return org.springframework.cloud.gateway.filter.ratelimit.KeyResolver * * 配置方法:参考网关过滤器的 RequestRateLimiter 配置项 */ @Bean public UserKeyResolver userKeyResolver() {
return new UserKeyResolver(); } / * @描述 获取请求地址的URL地址作为限流key * @作者 lixing * @日期 2021/7/17 14:26 * @Param [] * @return org.springframework.cloud.gateway.filter.ratelimit.KeyResolver * * 配置方法:参考网关过滤器的 RequestRateLimiter 配置项 */ @Bean @Primary public UrlKeyResolver urlKeyResolver() {
return new UrlKeyResolver(); } } / * @描述 基于ip进行限流 * @作者 lixing * @日期 2021/7/18 14:26 */ class HostAddressKeyResolver implements KeyResolver {
@Override public Mono<String> resolve(ServerWebExchange exchange) {
return Mono.just(Objects.requireNonNull(exchange.getRequest().getRemoteAddress()).getHostName()); } } / * @描述 基于用户id进行限流 * @作者 lixing * @日期 2021/7/18 14:26 */ class UserKeyResolver implements KeyResolver {
@Override public Mono<String> resolve(ServerWebExchange exchange) {
String token = exchange.getRequest().getHeaders().getFirst(SysKeyEnum.TOKEN.getKey()); if (!StrUtil.isEffective(token)) {
return Mono.just("default"); } try {
BaseLoginUserInfo baseLoginUserInfo = JwtUtil.verifyJwtForHs256(token); return Mono.just(baseLoginUserInfo.getAccount()); } catch (Exception e) {
return Mono.just("default"); } } } / * @描述 基于请求URL地址进行限流 * @作者 lixing * @日期 2021/7/18 14:26 */ class UrlKeyResolver implements KeyResolver {
@Override public Mono<String> resolve(ServerWebExchange exchange) {
return Mono.just(exchange.getRequest().getPath().value()); } } 网关配置
讯享网spring: # SpringCloud配置 cloud: # TODO 网关配置 gateway: # 路由机制 discovery: locator: # true 默认路由机制 # 开启服务注册和发现功能,服务网关自动根据服务发现为每一个服务创建一个路由,这个路由将以(大写服务名)开头的请求路径转发到对应的服务中 # 访问地址:127.0.0.1:8800/大写服务名/服务上下文/Controller/Method # # false 关闭默认路由机制,需要手动配置routes,默认通过路由名进行跳转的方式将失效,将请求路径上的服务名配置为小写 # 访问地址:127.0.0.1:8800/小写写服务名/服务上下文/Controller/Method enabled: false lower-case-service-id: true # 路由地址 routes: # TODO 基于 【BFF-AUTH】 服务的路由配置 - id: BFF-AUTH-ROUTE uri: lb://bffAuth predicates: - Path=/springCloudGateway/auth/ filters: # 自定义 [MyIpGatewayFilter] 网关过滤器。*表示允许所有ip请求,其它格式为:127.0.0.1,192.168.0.110 #- MyIp=127.0.0.1,192.168.1.1 # 自定义 [MyRequestParamsGatewayFilter] 过滤器。参数1:是否打印请求参数,参数2:是否解密请求参数 #- MyRequestParams=Y,Y - StripPrefix=1 - RewritePath=/auth/(?<segment>.*),/bffAuth/$\{
segment} # 请求限流 - name: RequestRateLimiter args: # 自定义限流字段解析器,当前对应UrlKeyResolver类进行配置 key-resolver: '#{@urlKeyResolver}' # 每秒向令牌桶添加1个令牌 redis-rate-limiter.replenishRate: 1 # 令牌桶最多存储10个令牌 redis-rate-limiter.burstCapacity: 10
网关整合Sentinel限流
<!-- FIXME ====================================================== SpringCloudGateway基于Sentinel网关限流的适配器 --> <dependency> <groupId>com.alibaba.csp</groupId> <artifactId>sentinel-spring-cloud-gateway-adapter</artifactId> </dependency> 路由维度限流(灵活性差,力度粗)
讯享网package com.springcloudalibaba.gateway.configurer; import com.alibaba.csp.sentinel.adapter.gateway.common.rule.GatewayFlowRule; import com.alibaba.csp.sentinel.adapter.gateway.common.rule.GatewayRuleManager; import com.alibaba.csp.sentinel.adapter.gateway.sc.SentinelGatewayFilter; import com.alibaba.csp.sentinel.adapter.gateway.sc.callback.BlockRequestHandler; import com.alibaba.csp.sentinel.adapter.gateway.sc.callback.GatewayCallbackManager; import com.alibaba.csp.sentinel.adapter.gateway.sc.exception.SentinelGatewayBlockExceptionHandler; import com.springcloudalibaba.bclass.base.BaseResult; import org.springframework.beans.factory.ObjectProvider; import org.springframework.cloud.gateway.filter.GlobalFilter; import org.springframework.context.annotation.Bean; import org.springframework.context.annotation.Configuration; import org.springframework.core.Ordered; import org.springframework.core.annotation.Order; import org.springframework.http.HttpStatus; import org.springframework.http.MediaType; import org.springframework.http.codec.ServerCodecConfigurer; import org.springframework.web.reactive.function.BodyInserters; import org.springframework.web.reactive.function.server.ServerResponse; import org.springframework.web.reactive.result.view.ViewResolver; import org.springframework.web.server.ServerWebExchange; import reactor.core.publisher.Mono; import javax.annotation.PostConstruct; import java.util.Collections; import java.util.HashSet; import java.util.List; import java.util.Set; / * @Description: TODO SpringCloudGateway基于Sentinel进行限流是通过Filter实现的。 * 需要向容器中注入SentinelGatewayFilter过滤器和SentinelGatewayBlockExceptionHandler异常回调 * @Author: lixing * @Date: 2020/11/21 15:40 */ @Configuration public class RequestRateLimiterForGatewaySentinelRouteConfig {
private final List<ViewResolver> viewResolverList; private final ServerCodecConfigurer serverCodecConfigurer; public RequestRateLimiterForGatewaySentinelRouteConfig(ObjectProvider<List<ViewResolver>> viewResolverListProvider, ServerCodecConfigurer serverCodecConfigurer) {
this.viewResolverList = viewResolverListProvider.getIfAvailable(Collections::emptyList); this.serverCodecConfigurer = serverCodecConfigurer; } // 初始化 SentinelGatewayFilter 过滤器 @Bean @Order(Ordered.HIGHEST_PRECEDENCE) public GlobalFilter sentinelGatewayFilter() {
return new SentinelGatewayFilter(); } // 初始化 SentinelGatewayBlockExceptionHandler 限流异常处理器 @Bean @Order(Ordered.HIGHEST_PRECEDENCE) public SentinelGatewayBlockExceptionHandler sentinelGatewayBlockExceptionHandler() {
return new SentinelGatewayBlockExceptionHandler(viewResolverList, serverCodecConfigurer); } // 自定义限流异常页面 @PostConstruct public void initBlockHandlers() {
BlockRequestHandler blockRequestHandler = new BlockRequestHandler() {
@Override public Mono<ServerResponse> handleRequest(ServerWebExchange serverWebExchange, Throwable throwable) {
return ServerResponse.status(HttpStatus.OK). contentType(MediaType.APPLICATION_JSON). body(BodyInserters.fromValue(new BaseResult<String>().fail("路由维度-触发流控"))); } }; GatewayCallbackManager.setBlockHandler(blockRequestHandler); } // 配置初始化限流参数 @PostConstruct public void initGatewayRules() {
Set<GatewayFlowRule> gatewayFlowRuleSet = new HashSet<>(); // 添加 BFF-AUTH-ROUTE路由 限流规则 gatewayFlowRuleSet.add( new GatewayFlowRule("BFF-AUTH-ROUTE") // 路由ID .setCount(1) // 限流阈值 .setIntervalSec(1)); // 统计时间窗口,默认单位秒 // 添加 BFF-ADMIN-ROUTE路由 限流规则 gatewayFlowRuleSet.add( new GatewayFlowRule("BFF-ADMIN-ROUTE") // 路由ID .setCount(1) // 限流阈值 .setIntervalSec(1)); // 统计时间窗口,默认单位秒 GatewayRuleManager.loadRules(gatewayFlowRuleSet); } }

自定义API维度限流(对请求路径进行分组,再对分组进行限流,灵活性好,粒度细)
package com.springcloudalibaba.gateway.configurer; import com.alibaba.csp.sentinel.adapter.gateway.common.SentinelGatewayConstants; import com.alibaba.csp.sentinel.adapter.gateway.common.api.ApiDefinition; import com.alibaba.csp.sentinel.adapter.gateway.common.api.ApiPathPredicateItem; import com.alibaba.csp.sentinel.adapter.gateway.common.api.ApiPredicateItem; import com.alibaba.csp.sentinel.adapter.gateway.common.api.GatewayApiDefinitionManager; import com.alibaba.csp.sentinel.adapter.gateway.common.rule.GatewayFlowRule; import com.alibaba.csp.sentinel.adapter.gateway.common.rule.GatewayRuleManager; import com.alibaba.csp.sentinel.adapter.gateway.sc.SentinelGatewayFilter; import com.alibaba.csp.sentinel.adapter.gateway.sc.callback.BlockRequestHandler; import com.alibaba.csp.sentinel.adapter.gateway.sc.callback.GatewayCallbackManager; import com.alibaba.csp.sentinel.adapter.gateway.sc.exception.SentinelGatewayBlockExceptionHandler; import com.springcloudalibaba.bclass.base.BaseResult; import org.springframework.beans.factory.ObjectProvider; import org.springframework.cloud.gateway.filter.GlobalFilter; import org.springframework.context.annotation.Bean; import org.springframework.context.annotation.Configuration; import org.springframework.core.Ordered; import org.springframework.core.annotation.Order; import org.springframework.http.HttpStatus; import org.springframework.http.MediaType; import org.springframework.http.codec.ServerCodecConfigurer; import org.springframework.web.reactive.function.BodyInserters; import org.springframework.web.reactive.function.server.ServerResponse; import org.springframework.web.reactive.result.view.ViewResolver; import org.springframework.web.server.ServerWebExchange; import reactor.core.publisher.Mono; import javax.annotation.PostConstruct; import java.util.Collections; import java.util.HashSet; import java.util.List; import java.util.Set; / * @Description: TODO SpringCloudGateway基于Sentinel进行限流是通过Filter实现的。需要向容器中注入SentinelGatewayFilter过滤器和SentinelGatewayBlockExceptionHandler异常回调 * @Author: lixing * @Date: 2020/11/21 15:40 */ @Configuration public class RequestRateLimiterForGatewaySentinelApiConfig {
private final List<ViewResolver> viewResolverList; private final ServerCodecConfigurer serverCodecConfigurer; public RequestRateLimiterForGatewaySentinelApiConfig(ObjectProvider<List<ViewResolver>> viewResolverListProvider, ServerCodecConfigurer serverCodecConfigurer) {
this.viewResolverList = viewResolverListProvider.getIfAvailable(Collections::emptyList); this.serverCodecConfigurer = serverCodecConfigurer; } // 初始化 SentinelGatewayFilter 过滤器 @Bean @Order(Ordered.HIGHEST_PRECEDENCE) public GlobalFilter sentinelGatewayFilter() {
return new SentinelGatewayFilter(); } // 初始化 SentinelGatewayBlockExceptionHandler 限流异常处理器 @Bean @Order(Ordered.HIGHEST_PRECEDENCE) public SentinelGatewayBlockExceptionHandler sentinelGatewayBlockExceptionHandler() {
return new SentinelGatewayBlockExceptionHandler(viewResolverList, serverCodecConfigurer); } // 自定义限流异常页面 @PostConstruct public void initBlockHandlers() {
BlockRequestHandler blockRequestHandler = new BlockRequestHandler() {
@Override public Mono<ServerResponse> handleRequest(ServerWebExchange serverWebExchange, Throwable throwable) {
return ServerResponse.status(HttpStatus.OK). contentType(MediaType.APPLICATION_JSON). body(BodyInserters.fromValue(new BaseResult<String>().fail("自定义路由API维度-触发流控"))); } }; GatewayCallbackManager.setBlockHandler(blockRequestHandler); } // 自定义API分组 @PostConstruct public void initCustomizedApis() {
Set<ApiDefinition> apiDefinitionSet = new HashSet<>(); / * 自定义 apiAuth_group1 分组 /springCloudGateway/auth/ */ ApiDefinition apiAuth_group1 = new ApiDefinition("apiAuth_group1").setPredicateItems(new HashSet<ApiPredicateItem>(){
{
// 添加断言,该值的内容为:配置文件spring.cloud.gateway.routes.predicates的值 + 自定义规则 add(new ApiPathPredicateItem().setPattern("/springCloudGateway/auth/demo/requestRateLimiter1/").setMatchStrategy(SentinelGatewayConstants.URL_MATCH_STRATEGY_PREFIX)); } }); / * 自定义 apiAuth_group2 分组 /springCloudGateway/auth/ */ ApiDefinition apiAuth_group2 = new ApiDefinition("apiAuth_group2").setPredicateItems(new HashSet<ApiPredicateItem>(){
{
// 添加断言,该值的内容为:配置文件spring.cloud.gateway.routes.predicates的值 + 自定义规则 add(new ApiPathPredicateItem().setPattern("/springCloudGateway/auth/demo/requestRateLimiter2/test1")); add(new ApiPathPredicateItem().setPattern("/springCloudGateway/auth/demo/requestRateLimiter2/test2")); } }); // apiDefinitionSet.add(apiAuth_group1); apiDefinitionSet.add(apiAuth_group2); GatewayApiDefinitionManager.loadApiDefinitions(apiDefinitionSet); } // 配置初始化限流参数 @PostConstruct public void initGatewayRules() {
Set<GatewayFlowRule> gatewayFlowRuleSet = new HashSet<>(); // 添加 apiAuth_test1分组 限流规则 gatewayFlowRuleSet.add(new GatewayFlowRule(("apiAuth_group1")).setCount(1).setIntervalSec(1)); // 添加 apiAuth_test2分组 限流规则 gatewayFlowRuleSet.add(new GatewayFlowRule(("apiAuth_group2")).setCount(1).setIntervalSec(1)); // GatewayRuleManager.loadRules(gatewayFlowRuleSet); } } 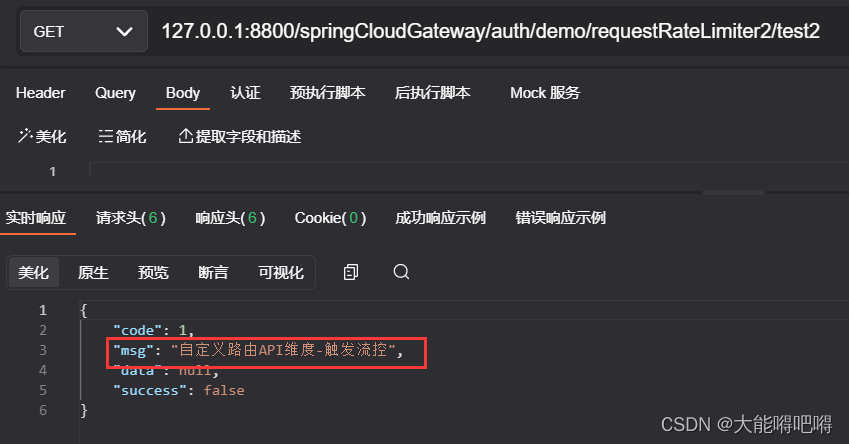

版权声明:本文内容由互联网用户自发贡献,该文观点仅代表作者本人。本站仅提供信息存储空间服务,不拥有所有权,不承担相关法律责任。如发现本站有涉嫌侵权/违法违规的内容,请联系我们,一经查实,本站将立刻删除。
如需转载请保留出处:https://51itzy.com/kjqy/116730.html